CISOs and technical evaluators are paid to distrust your marketing. In a high-stakes category where sales cycles span months, generic traffic is a vanity metric that masks a failing pipeline.
A successful cybersecurity SEO strategy treats organic search as pipeline infrastructure rather than a traffic game. The goal is to capture high-intent compliance queries and convert visibility into meetings through technical authority and AI-native credibility signals. This foundation ensures high-trust demand capture.
1. Dominate Compliance Intent to Capture Ready Buyers
Broad terms like cybersecurity services are often expensive traps that attract researchers rather than executives. An effective cybersecurity SEO strategy pivots to high-trust compliance queries like SOC 2, HIPAA, or CMMC. These signals indicate immediate urgency, executive scrutiny, and active vendor evaluation. Targeting these frameworks bridges the Technical Authority Gap by capturing buyers during the audit readiness phase.
Build a content map pairing frameworks with specific high-value industries:
- SOC 2 for SaaS and Fintech
- HIPAA for Healthcare providers
- CMMC or NIST 800-171 for Defense Manufacturing
- ISO 27001 for International Enterprise
Structure page types to transition from technical requirements to direct service mapping and proof assets. Include clear scope boundaries, audit-friendly language, and last updated dates to satisfy technical scrutiny and LLM trust signals. This shift transforms your keyword inventory into a prioritized pipeline infrastructure.
2. Engineer Trust Through Machine-Readable Technical Authority
Cybersecurity is trust-constrained. In a Zero Trust environment, both buyers and algorithms treat unverified claims as operational risks. To close the Technical Authority Gap, your expertise must be buyer-verifiable and machine-readable through concrete proof assets:
- Author Credentials: Link expert bios to verified CISSP, CISM, or OSCP certifications and professional profiles.
- Operations Pages: Document IR processes, escalation SLAs, and your tooling stack at a safe but credible level.
- Methodology-First Case Studies: Detail specific constraints and technical outcomes rather than using vague improved security phrasing.
Maintain editorial integrity by citing primary sources like NIST or MITRE advisories and providing visible update logs. This transparency transforms content into a technical briefing, accelerating BOFU conversions while signaling the authority required for rankings and AI citations.
3. Optimize for the Zero-Click Era and AI Citations
The search battlefield has shifted from blue links to direct citations in featured snippets and AI summaries. Security buyers scan for answers within AI Overviews rather than clicking through to technical pages. Your cybersecurity SEO strategy must prioritize content extraction to prevent losing demand to zero-click results. Making your site the default source captures visibility where traditional rankings fail.
Place a two-to-four sentence Answer Block at the top of technical pages to resolve queries immediately. Organize implementation steps into scannable sections with tables for clean AI parsing. Deploy essential schema to feed knowledge graphs:
- FAQPage for recurring technical questions
- Organization and Article for brand authority
- HowTo for implementation and deployment steps
Reinforce credibility with trust signals that AI models and CISOs prioritize:
- Clear published and updated dates
- Verified author credentials
- Inline citations for technical claims
This structure increases SERP real estate, improves CTR on high-intent queries, and bridges the Technical Authority Gap.
4. Differentiate Your Architecture: MSSP vs. SaaS SEO Playbooks
High-ranking cybersecurity sites often fail to generate meetings because they apply SaaS SEO playbooks to MSSP models. MSSPs sell trust, proximity, and compliance outcomes, whereas SaaS sells features, integrations, and documentation depth. Your cybersecurity SEO strategy must align with your specific sales motion to convert traffic into revenue.
A practical architecture split ensures your site drives qualified pipeline rather than vanity traffic:
- MSSP Focus: Service pages organized by compliance outcome and industry, local ecosystem pages, and how we deliver proof.
- SaaS Focus: Product-led feature pages, integration libraries, developer documentation, and competitive comparisons.
Success metrics also diverge. MSSP success relies on qualified consultations and RFP pipeline velocity, while SaaS prioritizes trial activations and PLG assists. Proper alignment ensures internal linking builds the topical authority necessary to bridge the technical authority gap in an AI-driven search landscape.
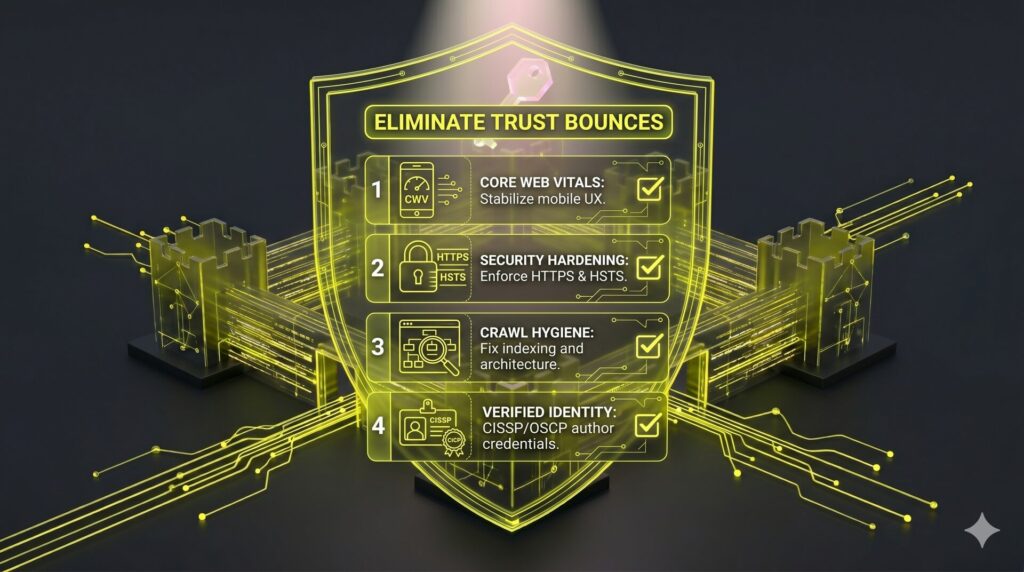
5. Harden Site Performance and Security to Eliminate Trust Bounces
CISOs and security buyers bounce instantly if a site feels compromised. Sluggish loading, broken SSL certificates, or aggressive tracking scripts are not just UX failures. They are credibility killers for firms selling protection.
Before scaling content, execute a trust baseline audit to ensure technical authority. Focus on:
- Core Web Vitals: Meet LCP and INP targets to maintain mobile stability.
- Crawl Hygiene: Fix canonicals, sitemap errors, and orphan pages to clarify site architecture for LLMs and search engines.
- Security Hardening: Enforce HTTPS via HSTS and implement a strict Content Security Policy (CSP) to mitigate third-party script risks.
Technical integrity removes ranking blockers and prevents friction on high-intent service pages. High-performing, secure infrastructure validates your domain expertise and increases conversion rates on BOFU pages before the discovery call.
6. Bridge the Authority Gap with Vulnerability Intelligence
Shallow news reporting fails to build trust. When critical vulnerabilities break, prospects require technical briefings that solve immediate risks rather than generic summaries. Publishing actionable guidance during these surges bridges the technical authority gap and captures high-intent traffic before the market saturates.
Use a rigid advisory template to signal real-time accuracy to CISOs and LLMs:
- Summary, affected versions, and CVSS severity.
- Confirmed exploit status.
- Mitigation steps and detection notes (IOCs/YARA).
Maintain trust through prominent timestamps, update logs, and direct links to primary sources like NVD or vendor advisories. Route readers from spike pages into evergreen how-to guides and service pages. This transformation turns volatile traffic into compounding pipeline infrastructure, positioning your firm as the definitive answer in an AI-driven landscape.
7. Scale Topical Depth with Programmatic Asset Portals
Manual production creates bottlenecks that leave cybersecurity brands invisible during market shifts. Relying on occasional deep-dives fails to cover the entity map required to close the Technical Authority Gap. Programmatic portals solve this by building massive topical depth through structured data.
Select portal types that align with your offer to avoid maintenance debt:
- Glossaries and academies (EDR, DSPM, Zero Trust).
- Compliance checklists and control mapping (NIST, SOC 2).
- Integration libraries (SIEM, SOAR, or IdP guides) for BOFU intent.
Every programmatic page must provide information gain through unique diagrams, examples, or decision criteria. Implement human fact-checks for technical details to maintain trust. Use consistent templates and strong hub-and-pillar linking to prevent thin content penalties.
This infrastructure creates a scalable authority engine. It supports traditional Google rankings while providing the structured data necessary for LLM citations and AI answer extraction.
8. Pivot from Link Placements to Technical Citations
Standard link building often fails because firms treat links as commodities rather than technical citations. In a mature cybersecurity SEO strategy, authority is earned through original contribution. Closing the Technical Authority Gap requires shifting from placements to creating defensible assets that experts naturally cite.
Build link-attracting assets that serve as primary sources for reporters and industry newsletters:
- Annual niche threat reports with a specific vertical or regional focus.
- Benchmark studies on response times or common audit misconfigurations.
- Sanitized incident learnings and methodology-backed what we saw reports.
Your promotion workflow must include a press summary page with embeddable charts and a methodology section to simplify citations. Providing unique data builds brand trust and ranking resilience in YMYL-adjacent search results. This strategy yields fewer total links but generates the high-authority signals necessary for durable pipeline growth.
9. Shift Focus from Tactical Implementation to Executive Risk
High-intent leads stall when content targets administrators instead of executives. A sophisticated cybersecurity SEO strategy translates technical depth into risk mitigation and business outcomes for the C-suite. While practitioners focus on troubleshooting, CISOs require:
- Decision frameworks and risk tradeoffs
- Vendor evaluation criteria
- Governance and maturity models
To bridge the Technical Authority Gap, produce high-performing formats like build-vs-buy guides, RFP checklists, and security program roadmaps. Map service controls to frameworks like SOC 2 or NIST to provide verifiable evidence of maturity. Include compliance-to-controls mapping to illustrate how your service covers and evidences specific security requirements.
This content functions as pre-sales enablement by answering late-stage questions regarding data handling, access controls, and reporting SLAs. Addressing these executive concerns reduces the prove-it drag in long cycles, improving lead quality and accelerating revenue capture.
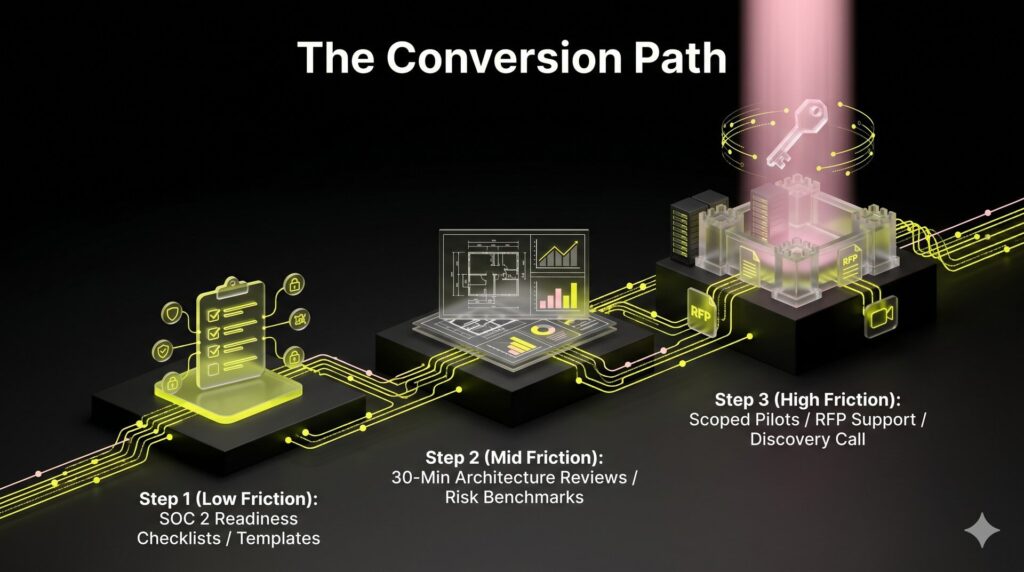
10. Implement a CTA Ladder to Capture Risk-Averse Buyers
High organic rankings mask a failing pipeline when the only next step is a high-stakes Contact Sales button. If your cybersecurity SEO strategy relies on a single bottom-of-funnel leap, you leak qualified leads not yet ready for a pitch. Bridge this Technical Authority Gap with a tiered CTA ladder:
- Low-friction: SOC 2 readiness checklists or control mapping templates to capture early intent.
- Mid-friction: 30-minute architecture reviews, compliance gap scans, or risk exposure benchmarks.
- High-friction: RFP support or scoped pilots for late-stage evaluation.
Support these CTAs with explicit trust signals by defining who the prospect will speak with and exactly what data is required. This structures the conversion path around technical intent, delivering higher lead quality and clearer revenue attribution than generic contact forms.
11. Leverage Geography and Ecosystems as Trust Accelerators
Enterprise buyers prioritize regional partners for response capability and jurisdictional fluency. In regulated sectors, local presence signals expertise in regional compliance nuances, closing the Technical Authority Gap. This provides a defensible wedge for MSSPs where competing for global head terms is often unrealistic.
Execute this local authority framework:
- Google Business Profile: Maintain consistent NAP data, accurate service categories, and localized Q&A to signal reliability.
- Geo-Vertical Pages: Build pages like MDR for Healthcare in [State] featuring localized compliance proof.
- Partner Ecosystems: Develop integration guides with SIEM or cloud partners to leverage their brand equity.
- Third-Party Validation: Link vetted directory listings, third-party analyst mentions, and regional case studies.
This infrastructure captures qualified inbound for region-specific queries. It also establishes the location-based entities required for Generative Engine Optimization (GEO), ensuring AI models cite your firm in localized security searches.
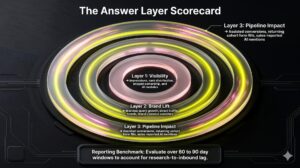
12. Replace Traditional SEO Reporting with Revenue Infrastructure Metrics
Executives ignore traffic growth when the sales pipeline remains stagnant. To bridge the Technical Authority Gap, replace vanity metrics with a revenue-first reporting system. Nuoptima treats a cybersecurity SEO strategy as pipeline infrastructure, focusing on:
- Qualified consults and demo requests
- Sales-accepted leads (SALs)
- Influenced pipeline value
Your measurement setup must define conversion events by funnel stage, from technical whitepapers to booked assessments. Track assisted conversions and time-to-close by content cluster to prove long-cycle contribution. Additionally, implement AI visibility tracking to monitor which queries trigger citations in answer engines like Perplexity or ChatGPT.
Execute a quarterly optimization loop for high-impression pages, prioritizing CISO-level compliance content that is almost ranking. This transforms SEO from a blog project into defensible revenue infrastructure that secures executive buy-in through measurable pipeline impact.
The 90-Day Cybersecurity SEO Roadmap: Building Revenue Infrastructure
Security marketing fails when teams prioritize publishing volume over technical trust. If your technical foundation is weak, search engines and AI models categorize your content as a liability rather than an authority. This roadmap provides the exact sequencing required to close the Technical Authority Gap and transform a site into a high-intent pipeline engine.
Prerequisites: Define Strategic Parameters (Before Day 1)
Content without a clear commercial map results in vanity traffic. Confirm these pillars before executing any technical or creative tasks.
1. Confirm the business model. Distinguish the cybersecurity SEO strategy based on whether the firm is an MSSP selling outcomes or a SaaS selling tools.
2. Define primary offers. List core revenue drivers such as MDR, vCISO, compliance auditing, or Incident Response.
3. Select target verticals. Identify high-stakes industries like FinTech, Healthcare, or Defense.
4. Define sales conversion events. Standardize what constitutes a Sales-Accepted Lead (SAL) versus a generic whitepaper download.
Days 0 to 30: Build the Technical Trust Baseline
Phase one focuses on hardening infrastructure to satisfy both CISOs and search algorithms. You must eliminate trust bounces by following these steps.
1. Audit site health. Resolve Core Web Vitals (CWV) blockers and stabilize mobile UX to prevent high bounce rates.
2. Harden site security. Verify HTTPS, implement HSTS, and remove risky third-party scripts to protect the domain’s reputation.
3. Clean the crawl path. Tighten internal linking and resolve indexing errors. This simplifies the site architecture for LLM discovery and traditional crawling.
4. Standardize technical identity. Update author bios with verified credentials like CISSP or OSCP. Publish dedicated Proof Pages featuring client case studies and specific security methodologies.
Expected Outcome: You will achieve a secure, audit-ready site foundation with zero critical technical errors.
Days 31 to 60: Launch the High-Trust Content Engine
Once the foundation is secure, pivot to high-intent keyword mapping. Target buyers with immediate urgency using a compliance-first approach.
1. Deploy money pages. Publish 3 to 5 pages targeting compliance frameworks like SOC 2, NIST, or HIPAA filtered by your target vertical.
2. Create executive assets. Build 2 high-level assets for the C-suite. Use formats like an RFP checklist or a security maturity model.
3. Release practitioner guides. Publish 3 implementation guides or technical briefings for practitioners to build technical authority.
4. Apply GEO formatting. Add answer blocks, structured tables, and FAQ schema to every page. You will see your content appearing in AI answer engine previews and featured snippets.
Expected Outcome: Content clusters will index for primary compliance terms and generate initial citations in AI summaries.
Days 61 to 90: Scale Authority and Distribution
The final phase shifts from content creation to authority building and real-time incident response.
1. Release original research. Publish one data-backed asset, such as a niche threat report. This earns high-authority backlinks and technical citations.
2. Launch a programmatic portal. Build a glossary or integration library with strict technical QA. This captures broad informational intent at scale.
3. Establish a news response workflow. Create a process for publishing CVE technical briefings within 24 hours of a major security incident.
Expected Outcome: You will see a measurable increase in inbound backlink quality and a spike in brand-related AI citations.
Success Criteria: Measuring Revenue Impact
By Day 90, ignore generic traffic volume. Measure success through revenue-centric metrics. The roadmap is successful if you achieve ranking movement on compliance-specific terms, an increase in qualified conversion events from organic search, and a measurable presence in AI summaries for high-intent queries. This framework ensures your cybersecurity SEO strategy remains a defensible revenue system.
FAQ
Cybersecurity SEO carries a much higher burden of proof due to its high-stakes, YMYL-adjacent nature. Standard B2B SEO often prioritizes top-of-funnel traffic volume, but security buyers and algorithms require extreme accuracy and verified professional authorship. Success in this niche is measured by pipeline influence and MQL quality rather than raw hits. Since technical evaluators are trained to be skeptical, every content asset must serve as a primary trust signal. See section two for more on building technical authority.
The primary difference lies in the intent behind the search. MSSP SEO focuses on service-led outcomes, regional trust, and specific local ecosystem needs. SaaS SEO targets product-led features, software integration depth, and technical documentation. While an MSSP needs to rank for compliance-driven managed security queries, a SaaS provider prioritizes feature-specific keywords and comparisons. Use the MSSP playbook if your revenue depends on expert delivery and the SaaS playbook for tool-based solutions. See section four for the full breakdown.
You can demonstrate expertise through sanitized narratives that focus on methodology and technical outcomes rather than exposing specific client identities. Use anonymized case studies that detail the architectural decisions and frameworks used during a successful incident response. Highlighting team credentials, third-party certifications, and clear data handling statements also builds trust without creating operational risks. Providing visible update logs and citing primary sources like NIST or MITRE further validates your authority to buyers and search engines.
Only publish CVE or vulnerability content if you can provide accurate, actionable mitigation steps for your specific audience. If you cannot offer unique information gain, focus on a lightweight response format that cites primary sources like the NVD or vendor advisories. Use a relevance triage process to decide which vulnerabilities affect your core client verticals. This approach allows you to capture high-intent search surges during incidents without maintaining a dedicated threat research department. Refer to section six for details.
Generative Engine Optimization (GEO) does not replace traditional SEO. It acts as an additional layer of technical formatting and distribution on top of established topical authority. While SEO focuses on visibility in traditional search results, GEO ensures your brand is the cited answer in AI-generated summaries and answer engines. Treat AI visibility as a practical metric. Track your LLM citations alongside traditional rankings and conversion events to ensure your firm remains the definitive answer in an AI-driven landscape.

![ChatGPT SEO [ Master the Answer Layer and Google Rankings ]](https://nuoptima.com/wp-content/uploads/2026/05/ChatGPT-SEO-300x167.png)