Enterprise decision-makers do not buy technical features. They invest in risk mitigation and operational governance. Most MSP pages fail to convert because they prioritize vanity traffic over high-intent questions about cost and Day-2 ownership. To rank for cloud migration services while winning over Private Equity partners, your page must act as a strategic asset. This checklist bridges the technical authority gap. Start by answering what is cloud migration services? in buyer language to earn trust through proof and decision criteria.
1. What Are Cloud Migration Services? Defining Scope and Deliverables
Enterprise IT leaders often inherit migration projects that spiral into financial drains due to vague scoping. To protect EBITDA and ensure M&A readiness, you must define cloud migration services through operational deliverables rather than marketing fluff. Technical authority is established by identifying specific workload requirements before the first byte moves.
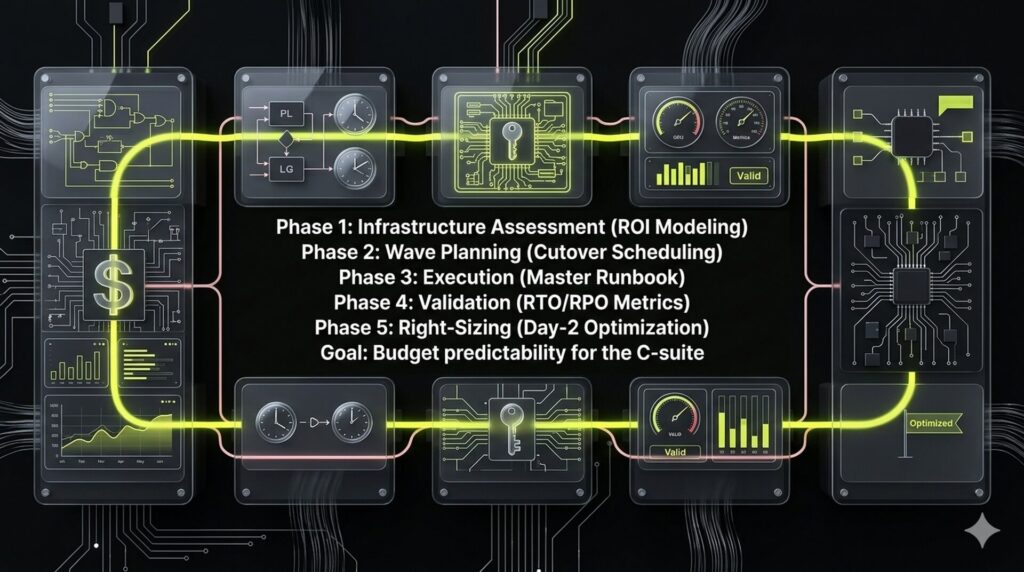
Standard migration services follow a structured lifecycle: infrastructure assessment with ROI modeling, cutover planning, execution, validation, and post-migration right-sizing. Unless explicitly scoped, these engagements do not include application code rewrites, data governance redesigns, or comprehensive security program overhauls. These exclusions prevent project delays and ensure budget predictability for the C-suite.
Enterprise Scope Clarity
- Workload Types: VMs, SQL/NoSQL databases, M365 tenant moves, VDI, and line-of-business apps.
- Platforms: AWS, Azure, and GCP, including hybrid constraints and shared-responsibility boundaries.
- Deliverables: A validated environment meeting specific compliance standards (SOC2/HIPAA) and rigorous uptime SLAs.
Defining these boundaries early bridges the technical authority gap and transforms your IT infrastructure into a high-valuation asset.
2. A Scalable Methodology: How Our Cloud Migration Services Work
Enterprise buyers prioritize predictability to protect asset value. Haphazard transitions create technical debt that complicates M&A due diligence. We utilize a structured five-phase framework to de-risk the move and ensure auditability.
How Our Cloud Migration Services Work
- Discovery and Dependency Mapping: We inventory all assets and map application groupings. This prevents service disruptions and ensures the migration ROI model remains accurate.
- Strategy and Wave Planning: Applications are assigned a path: rehost, replatform, or refactor. We build wave plans that migrate low-risk workloads first to build momentum.
- Execution via Master Runbook: We minimize downtime using defined cutover windows and a master runbook. This provides stakeholders with a clear audit trail and predictable results.
- Security and Compliance Gates: Workloads must clear strict security gates before going live. This maintains HIPAA or SOC2 standards throughout the transition.
- Validation and Rollback Readiness: Success is measured against specific RTO and RPO metrics. Every migration includes a tested rollback plan to guarantee business continuity.
3. Beyond the Quote: Proactively Managing Enterprise Cost Drivers
Enterprise migration budgets rarely fail because of the migration itself. Instead, opaque cost drivers catch leadership off-guard, eroding technical authority and stalling deals. To protect EBITDA growth and maximize enterprise valuation, we address these financial friction points proactively.
Enterprises typically encounter three hidden cost traps that derail ROI:
- Data Egress Scenarios: Unexpected fees from cross-region or inter-service transfers during initial synchronization.
- Double-Run’ Overlap: The inevitable window where you fund legacy hardware and cloud infrastructure simultaneously.
- Licensing Risks: Dual-licensing requirements and conversion costs during the transition phase.
We replace static price lists with a discovery-driven estimation framework. To produce a high-fidelity estimate range, we analyze:
- Inventory and utilization metrics
- Compliance constraints
- Downtime tolerance
This output includes specific assumptions grounded in operational reality. Such transparency ensures cloud migration services are viewed as a strategic asset rather than an uncontrolled liability.
4. Selecting the Stack: Native Tools vs. Third-Party Flexibility
Technical successes often become operational liabilities due to tool-first approaches that ignore vendor lock-in and sprawl. This Technical Debt reduces M&A readiness and complicates future exits. A defensible cloud migration services strategy requires a clear hierarchy to balance migration speed with long-term agility.
We follow a Native-First escalation path to maintain cost control. For single-destination moves into AWS, Azure, or GCP, native tools maximize integration while minimizing licensing fees. We only escalate to specialized third-party solutions for complex legacy refactoring, multi-cloud reporting, or vendor-agnostic requirements.
To protect enterprise valuation, we maintain portability through Infrastructure as Code (IaC) standards like Terraform. This ensures your infrastructure remains a transferable asset with clear data export pathways. Every transition is verified through pre-cutover validation pilots and data integrity checks to eliminate risks before the final sync.

5. Risk Mitigation: Maintaining Compliance During Cloud Migration
Enterprise migration is fundamentally a risk management exercise where the primary threat to valuation is the transition-phase compliance gap. Parallel environments and temporary administrative access often elude standard auditing, compromising M&A readiness. Maintaining compliance during cloud migration is essential to prevent failed audits during technical due diligence and preserve your exit readiness.
We mitigate these risks by mapping technical controls to the migration lifecycle:
- Least Privilege: Restricting administrative access to the minimum necessary for transition tasks.
- Encryption: Enforcing end-to-end protection for sensitive data at rest and in transit.
- Audit Evidence: Maintaining log retention, configuration baselines, and rigorous change management.
These controls provide the audit trails required for HIPAA, PCI-DSS, or SOC 2 integrity during cutover. Your final decision should hinge on the post-cutover shared responsibility model. You must determine who owns security controls long-term, whether managed internally or through specialized cloud migration services, to ensure continuous oversight. A secure transition ensures your cloud infrastructure remains a compliant, [investment-grade asset](placeholder) that survives investor scrutiny.
6. Day-2 Operations: Transforming Migration into Operational Equity
Technical migrations often fail when providers treat the cutover as a finish line. While competitors focus solely on the move, enterprise leaders buy operational ownership to protect their investment. High-value cloud migration services bridge this gap by packaging Day-2 governance into the strategy, ensuring the platform remains a scalable asset rather than an operational liability.
We define concrete Day-2 deliverables to maintain long-term health and visibility:
- Security & Maintenance: Automated patching cadences, vulnerability management, and proactive alerting.
- Infrastructure Optimization: Continuous rightsizing and performance tuning to eliminate over-provisioning.
- FinOps Governance: Strict budget enforcement, anomaly alerts, and tagging standards for investor-ready financials.
This ownership is formalized through SLAs defining response times, escalation paths, and shared on-call models. These frameworks reduce incident noise and cut cloud waste while stabilizing environment performance. Shifting focus to ongoing governance transforms cloud infrastructure into a stabilized asset that directly supports EBITDA growth and M&A readiness.
How to Build a High-Converting Cloud Migration Services Page
Transform technical complexity into a high-intent conversion engine by following this execution sequence. This structure aligns your cloud migration services with the procurement needs of enterprise buyers and Private Equity partners to maximize EBITDA protection.
Step 1: Set Your Strategic Prereqs
Define technical boundaries before writing any copy. Select your primary Ideal Customer Profile (ICP), such as a PE-backed growth firm or a compliance-heavy global enterprise. Commit to a specific cloud destination like AWS or Azure and choose a default migration motion: rehost, replatform, or refactor.
Expected Outcome: You prevent scope creep and establish immediate technical authority.
Step 2: Sequence the Page Layout
Organize the page to address risk management and governance before features. Start with an above-the-fold outcome focused on downtime minimization and risk reversal. Follow with a clear definition of your cloud migration services and a methodology section that explicitly includes rollback protocols. Insert a TCO reality check and a tools comparison table to provide transparency.
Expected Outcome: The prospect sees a structured, low-risk path to migration that simplifies their decision-making process.
Step 3: Define Day-2 Operations
Detail your post-migration support package and Service Level Agreements (SLAs). Use this section to shift the buyer’s perspective from a one-time project to long-term organic equity and governance.
Expected Outcome: You move the lead from a project mindset to a managed partnership, increasing potential Lifetime Value.
Step 4: Deploy Procurement Proof Assets
Reduce friction in the final approval stage by providing concrete documentation. Embed a case study snippet demonstrating a successful compliance transition and offer a redacted runbook as a downloadable sample.
Expected Outcome: You satisfy the due diligence requirements of technical owners and procurement leads, accelerating the sales cycle.
FAQ
Cloud migration services are specialized technical engagements designed to move digital assets, databases, and applications from legacy environments to a cloud provider. A standard program follows a structured lifecycle: discovery, wave planning, technical execution, validation, and post-migration optimization. While infrastructure moves are standard, optional services typically include application code refactoring, advanced security posture redesigns, and comprehensive compliance auditing. See Section 1 above for a full scope breakdown.
Pricing typically follows a discovery-led model driven by workload volume and data complexity. Major cost drivers include infrastructure size and specific compliance requirements. Enterprises must account for hidden expenses such as data egress fees, licensing transitions, and the unavoidable double-run overlap where both environments are billed simultaneously. We recommend a full inventory audit to produce an accurate, investment-grade estimate that protects your EBITDA.
Timelines vary significantly based on application count, dependency density, and your specific downtime tolerance. A typical enterprise migration usually spans three to nine months. To maintain business continuity, we recommend a pilot-first approach followed by migration waves. This incremental strategy allows for performance validation and risk mitigation before moving mission-critical systems, ensuring the project remains on schedule and within budget.
The choice depends on your balance between immediate speed and long-term asset valuation. Lift-and-shift (rehosting) is the fastest route for urgent data center exits. Replatforming offers a middle ground by modifying the OS or database for cloud benefits. Refactoring provides the highest long-term value by re-architecting for cloud-native features. Most enterprise programs use a mixed strategy tailored to the specific strategic importance of each application.
Post-cutover, or Day 2 operations, focuses on stabilizing the environment to protect enterprise equity. This phase includes continuous security patching, FinOps governance to prevent cost sprawl, and performance tuning. A formal ownership model and Service Level Agreements (SLAs) are essential to prevent handoff chaos. This ensures the new infrastructure remains a compliant, high-performance asset rather than an unmanaged operational liability.
Scale and protect your digital infrastructure with NUOPTIMA.



