Vague technical lists kill conversion rates on MSP service pages. To capture high-intent traffic for network support services, your site architecture must bridge engineering with business-critical outcomes like uptime, low latency, and security. This checklist moves beyond generic networking theory. It is a strategic mapping tool for MSPs to align technical headers with local search intent and M&A readiness. These high-impact service components prioritize performance metrics that directly drive qualified, bottom-funnel leads.
1. The Strategic Network Assessment: Eliminating Reactive “Band-Aid” Support
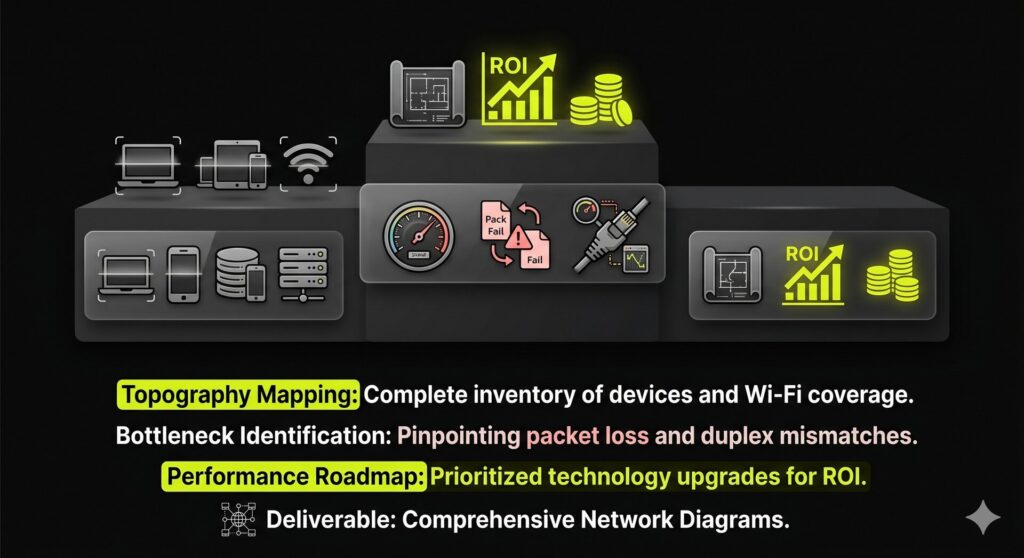
Sluggish performance often persists because providers treat symptoms instead of underlying infrastructure failures. Strategic network support services prioritize comprehensive discovery and inventory over reactive fixes. This assessment maps topology, device roles, and Wi-Fi coverage to identify the 20% of issues causing 80% of bottlenecks. We pinpoint specific failures like duplex mismatches, oversubscribed uplinks, and aging firewalls that stall productivity.
Our assessments replace vague IT promises with performance-focused deliverables:
- Comprehensive network diagrams
- Detailed bottleneck reports
- Prioritized technology roadmaps
Hard metrics like packet loss and latency prove ROI to technical stakeholders. Localized on-site assessments are available in [City/County] to ensure a predictable, high-performance environment.
2. Proactive Network Monitoring: Shifting from Reactive Fixes to Infrastructure Prevention
Traditional network support services focus on fixing what is already broken. We transform this into a prevention engine by continuously monitoring WAN uptime, firewall health, and switch status. This identifies ISP flaps, AP overloads, or failing ports before they impact productivity.
Our performance management includes:
- Real-time tracking of throughput, latency, and packet loss.
- Defined response-time targets mapped to alert severity.
- Automated triage from initial alert to ticket resolution.
Monthly reports include sections for WAN Availability, Firewall Security, and Device Health to ensure measurable accountability. For businesses in [City/Region], we provide on-site escalation for critical outages within our service radius. We explicitly state all coverage limits and exclusions to ensure your infrastructure remains a high-performance asset.
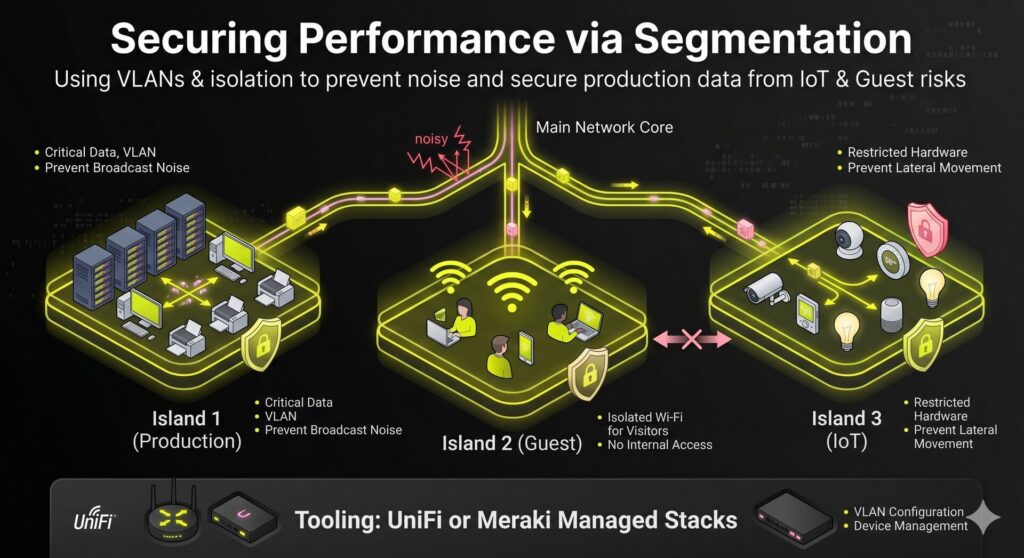
3. Network Segmentation: Securing Performance Through Logical Isolation
Compromised IoT devices or guest streaming should never jeopardize production data or saturate mission-critical bandwidth. Flat networks increase security risks and degrade performance through excessive broadcast noise.
Our network support services implement logical isolation using VLANs, dedicated SSIDs, and inter-VLAN firewall rules for automated policy enforcement. This ensures cleaner traffic flows and stronger security by:
- Isolating guest Wi-Fi from internal printers and servers.
- Restricting IoT hardware to prevent lateral movement risks.
- Applying Quality of Service (QoS) to prioritize critical traffic.
We manage staged rollouts using SMB-standard stacks like UniFi or Meraki to guarantee zero disruption. For clinics, retail, or manufacturing in [City], this architecture is a baseline requirement for regulatory compliance and long-term infrastructure stability.
4. Managed Wi-Fi Optimization: Solving the “Full Bars, No Data” Dilemma
Why does your device show full bars while your Zoom call freezes? This “full bars, no data” symptom typically stems from RF interference, over-channelization, or overloaded access points rather than a lack of coverage. Our network support services treat wireless as an engineered outcome. We focus on technical levers including coverage planning, channel width selection, transmit power tuning, and roaming standards.
This approach eliminates dead zones and ensures stable connectivity for mobile users in [City] offices and warehouses. Our on-site wireless assessments provide:
- Post-survey RF heatmaps to visualize signal hygiene.
- Performance baselines for latency and throughput.
- Configuration logs for hardware tuning and SSID design.
Stop reacting to connection drops and start measuring performance.
5. Internet Edge Resilience: Protecting Continuity Beyond the LAN
High-speed switches provide little value if a single ISP link creates a persistent point of failure. Our network support services stabilize the internet edge to eliminate full-stop outages, shifting focus beyond the LAN to the gateway. This design-led approach ensures business-critical tools remain predictable during carrier disruptions.
Our resilience framework includes:
- Redundant Connectivity: Dual-ISP circuits with automated LTE/5G failover policies.
- Traffic Prioritization: Granular QoS rules for VoIP, conferencing, and ERP traffic.
- Carrier Coordination: Direct management of provider relations and SLA-backed failover.
We support HQ and branch offices across [Metro Area] with a scope covering infrastructure design and implementation. Our SLAs define failover triggers, protecting productivity without manual intervention.
6. Hybrid Network Architecture: Balancing Performance and Fiscal Predictability
Avoid the “all-or-nothing” infrastructure trap. Our network support services utilize a pragmatic hybrid approach, keeping low-latency applications and regulated data on-prem while leveraging the cloud for backups and burst workloads. This strategy balances predictable CapEx with the OpEx flexibility CFOs require, effectively avoiding cloud egress spikes and on-site overprovisioning.
Deployment requires evaluating these critical decision factors and deliverables:
- Workload stability and egress cost models
- Data residency and compliance requirements
- Secure connectivity via VPN or encrypted tunnels
- Unified monitoring across local and remote environments
We provide local on-site support for core infrastructure alongside remote management for cloud services. This ensures your primary systems maintain raw LAN speeds while the broader network remains scalable, modern, and resilient.
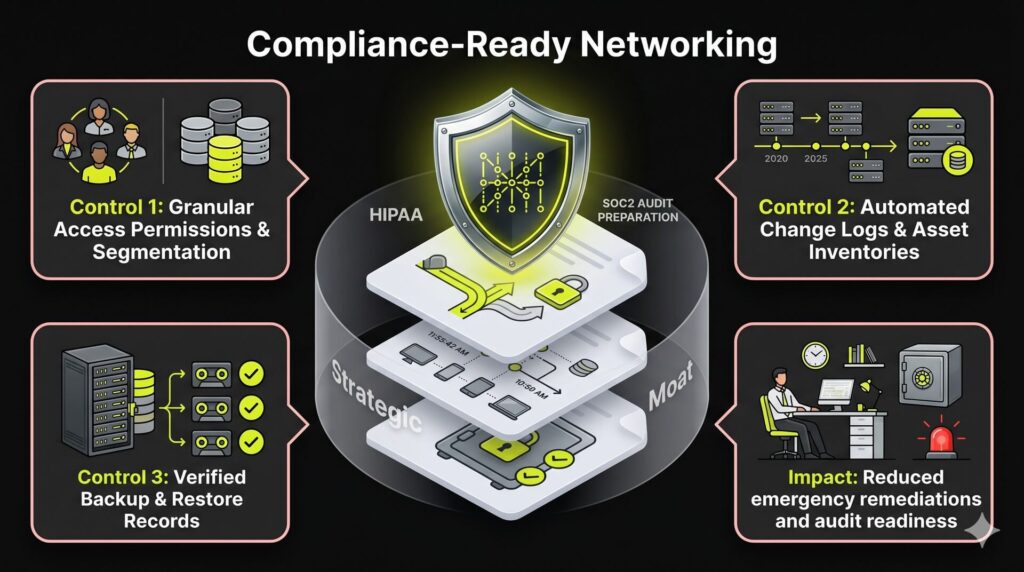
7. Compliance-Ready Networking: Documentation as a Strategic Moat
Regulatory readiness should not trigger a scramble for missing logs during a surprise audit. High-performance network support services must function as a continuous evidence engine. We implement technical controls including granular access permissions, logical segmentation, and strict patch cadences to satisfy frameworks such as HIPAA or SOC2.
We maintain the technical controls while your leadership handles governance. To support your compliance program, we provide:
- Automated change logs and asset inventories.
- Vulnerability and patch reporting.
- Verified backup and restore records.
Standardizing these controls eliminates chaotic changes and reduces emergency remediations. We deliver specialized HIPAA-focused IT network support services in [City] to help local firms transform technical documentation into a market-leading differentiator.
How to Build a High-Converting Network Support Service Page
Stop building bloated pages that fail to rank. Follow this execution schedule to build a high-performance cluster that captures local and service-specific intent.
Step 1: Define Primary Page Intent
Target network support services on your anchor page. Establish this page as a commercial and informational hybrid to build authority before the sales call. Ensure the URL structure reflects a clear service hierarchy.
Step 2: Map Secondary Keyword Variants
Group secondary phrases to prevent keyword cannibalization. Treat it network support services and computer network support services as on-page H3 variants. Use search data to confirm if distinct intent requires separate pages.
Step 3: Layer Local SEO Signals
Build one core service page supported by location pages for areas with physical coverage. Include map embeds, localized testimonials, and onsite response radii. These elements provide essential proof for high-intent MSP buyers.
Step 4: Configure Conversion Blocks
Bridge the technical authority gap with targeted content modules. List specific inclusions, severity-based SLA response times, and supported hybrid environments. Highlight specialized experience in industries like finance or healthcare. Add reporting samples and case-study placeholders to drive conversion.
Step 5: Implement Schema and Trust Basics
Deploy LocalBusiness and Service schema to become a primary citation for generative engines. Maintain strict NAP consistency across directories and implement a review strategy to increase organic equity and enterprise valuation.
Checklist Summary
- Primary keyword intent set
- Local proof elements integrated
- SLA and vertical blocks active
- Schema validated
FAQ
The choice depends on your operational model. Per-user pricing is ideal for office teams where employees use multiple devices, such as a laptop, mobile, and tablet. Per-device pricing fits environments with shared hardware, including POS systems, kiosks, or industrial machinery. Most modern MSPs favor per-user models to provide predictable monthly billing and simplify license management for the client. See Section 6 for more on balancing performance with fiscal predictability.
A professional provider should offer tiered response times based on incident severity. A P1 critical outage should trigger a response within 15 to 60 minutes. It is vital to differentiate between “response” (the time to acknowledge the ticket) and “resolution” (the time to fix the issue). Professional agreements should also specify on-site arrival times for hardware failures within a defined local service radius to ensure business continuity.
Not necessarily. On-prem infrastructure typically offers lower latency for high-bandwidth local workloads, but cloud services provide superior scalability and remote accessibility. A hybrid approach is often the most practical middle ground for balancing raw performance with operational flexibility. Be wary of hidden cloud expenses such as data egress fees and ensure strict governance is in place to prevent unpredictable budget overruns and “cloud sprawl.”
To dominate local search, include service-area specificity and consistent NAP (Name, Address, Phone) data. Add localized reviews, client testimonials, and case study snippets from your specific region. Avoid generic doorway pages: ensure every location-specific page provides unique operational proof and relevant calls to action. This builds the technical authority necessary to convert high-intent local traffic into qualified leads.
Compare the total cost of ownership rather than just the base retainer. Ask for a detailed list of exclusions, onboarding fees, project costs, and after-hours rates. Verify the specific security tooling included in the scope and the cadence of technical reporting. Look for clearly documented escalation paths to ensure you have direct access to senior engineering talent during a network crisis. This kind of structured evaluation reflects a more disciplined, outcome-focused approach, similar to how NUOPTIMA approaches performance and accountability.



