Audit pressure or board-level risk often forces a reactive search for IT compliance services, yet treating this as a one-time project ensures future failure. High-growth firms require an operational system of controls, evidence, and accountability. This guide offers seven criteria to evaluate partners, including managed IT compliance services, ensuring they provide clear framework mapping and defined audit boundaries. We start with the most common failure point: the lack of a structured shared responsibility model.
1. Demand a Formalized Shared Responsibility Model
Compliance failures often stem from a compliance gap where clients assume the provider owns the entire risk profile. Audits often reveal missing policy approvals or risk acceptances, which can stall M&A readiness or certifications. Demand that IT compliance services provide a written Shared Responsibility Model (SRM) mapped to your specific framework or control family. This eliminates the false assumption that outsourcing technical tasks equals outsourcing legal liability.
A robust SRM defines boundaries for all in-scope systems:
- Cloud accounts and SaaS environments
- Endpoints and on-premise hardware
- Backups and logging protocols
During evaluation, ask: Which controls are operationally managed by you versus attested by us? and What evidence do you produce versus what must we generate? Defining these roles ensures the provider handles technical execution while you maintain governance. This structure prevents we thought you had that gaps during incidents and creates a comparable basis for auditing vendors.
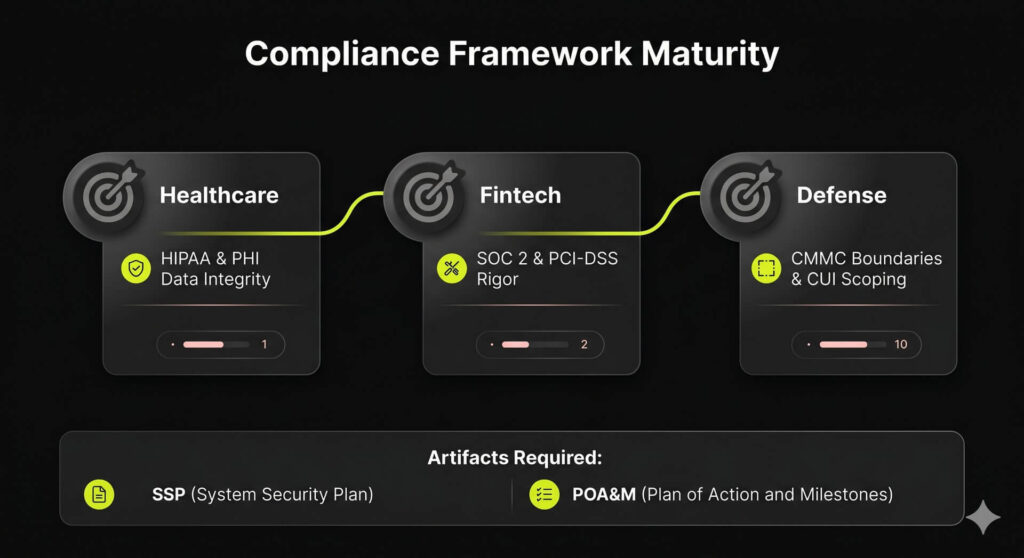
2. Verify Framework-Specific Depth and Vertical Maturity
Selecting a provider with general expertise is a gamble that risks audit failure. A provider excelling in SOC2 often lacks the technical depth required for defense supply chain standards. High-value IT compliance services require framework-specific depth rather than generic checklists to bridge the technical authority gap.
Verification should prioritize two critical areas:
Vertical Maturity: Deep experience in healthcare, fintech, or defense to manage sector-specific data types, audit rigor, and vendor risks.
Full-Service Lifecycle: Capabilities must include gap assessments, control implementation, evidence collection, and direct audit support.
For CMMC, due diligence must be granular to ensure investor-grade scrutiny. Ask how they scope CUI boundaries and if their internal tooling enters your assessment boundary. Verify they produce mandatory artifacts like the System Security Plan (SSP) and Plan of Action and Milestones (POA&M) instead of merely advising. This ensures your partner can realistically support audit expectations while building organic equity in your compliance posture.
3. Prioritize Tangible, Audit-Ready Deliverables Over Passive Monitoring
Don’t pay for passive monitoring that fails to produce audit-ready evidence. Many IT compliance services promise constant oversight but leave internal teams scrambling for artifacts during an audit. To protect enterprise valuation and M&A readiness, buyers must prioritize measurable outputs that auditors and leadership can consume immediately.
Request these specific deliverables to ensure technical effort translates into investor-grade evidence:
- Control-to-Evidence Mapping: Documentation linking technical configurations directly to specific regulatory framework requirements.
- Recurring Compliance Reports: Summaries of exceptions, risk register items, remediation status, and maturity trendlines for C-suite review.
- Audit-Ready Export Packages: Compiled, time-stamped artifacts supported by narrative notes that provide essential data context.
The final proof test is requesting a redacted sample dashboard or reporting pack. Evaluate the format and clarity to ensure it aligns with your leadership’s reporting needs. If a provider cannot demonstrate professional, consumable evidence, they are selling administrative effort rather than actionable compliance outcomes.
4. Insist on Technical Integrations That Operationalize Compliance
Hiring a provider who advises but cannot operationalize compliance creates a Technical Authority Gap. Without deep integrations, managed becomes a euphemism for manual evidence gathering that drains internal resources. True managed IT compliance services must connect directly to your stack to automate evidence capture and coverage. This ensures continuous control and transforms compliance into operational leverage.
Your partner should provide an integration roadmap across these operational layers:
- Identity: SSO, MFA, and IdP for access lifecycle.
- Infrastructure: Cloud platforms and endpoint management.
- Operations: Ticketing, PSA, and SIEM logging.
- HRIS: Automating employee onboarding and offboarding evidence.
Leveraging automation platforms ensures technical configurations become real-time artifacts. When evaluating partners, ask: Which integrations are native versus custom scripts? and How do you handle maintenance when APIs change or new apps are added? This confirms if a provider can truly sustain your posture as a strategic asset not a manual burden.
5. Validate the Service Delivery Framework: Roles, Cadence, and Escalations
Compliance retainers often look like high-performance engines during sales calls but stall during audits. This failure is rarely technological; it is a breakdown in delivery mechanics. Unclear roles and weak SLAs create gaps that result in missed deadlines and audit surprises.
When evaluating IT compliance services, demand transparency regarding staffing. Ensure the provider assigns specific personnel for these functions:
- Compliance Lead: Manages frameworks and documentation.
- Security Engineers: Handle technical execution.
- vCISO: Provides strategic advisory.
Verify the operational cadence. A reliable provider must commit to monthly evidence reviews, quarterly risk assessments, and a fixed control testing schedule.
Define the escalation path. Confirm how exceptions become tickets and establish clear time-to-resolution targets. Request a sample 30/60/90-day onboarding plan tied to measurable outputs. Without these mechanics, IT compliance services are a marketing promise rather than a predictable growth asset.
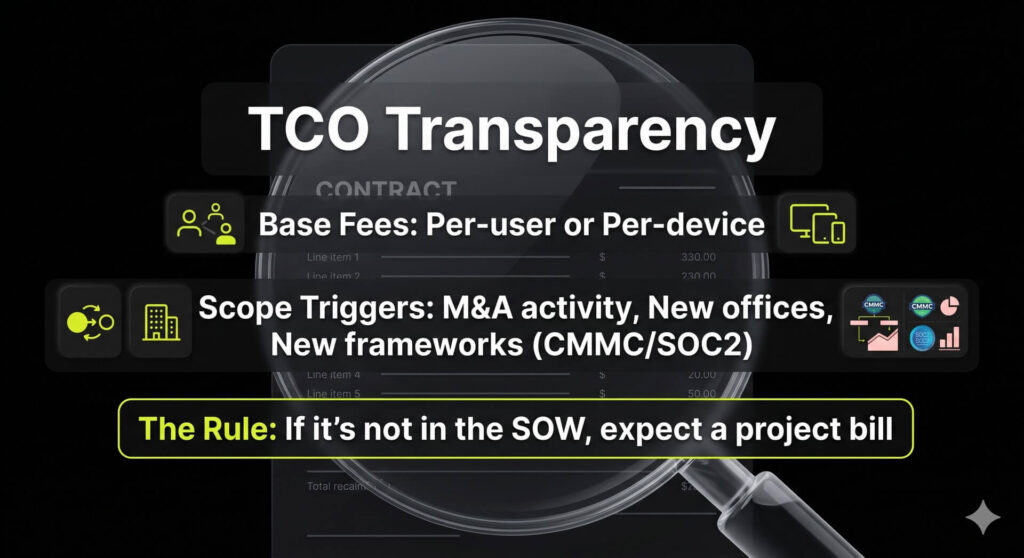
6. Insist on Pricing Transparency and Comprehensive Scope Mapping
Fixed-price quotes often balloon when providers fail to bridge high-level advisory with technical remediation. Treating IT compliance services as sporadic projects creates budget shock and unsustainable scope creep. To protect margins and EBITDA, you must demand transparency across pricing models.
Most providers utilize one of these structures:
- Per-user or per-device base fees with compliance add-ons.
- Tiered service packages (e.g., Basic vs. Premium).
- Flat-rate bundles or project-based assessments.
Evaluate total cost by requiring a line-item scope map covering assessment, remediation, tooling, and audit support. Ask which triggers lead to price adjustments:
- New office locations or M&A activity.
- Adopting new frameworks like CMMC or SOC2.
- SLA upgrades or increased reporting frequency.
Standardizing these variables turns compliance into a predictable investment rather than a financial surprise. Use a compliance services scope template to compare vendors on an apples-to-apples basis and prevent hidden add-ons from appearing post-signature.
How to Build Your IT Compliance Services Selection Scorecard
Selection failures are rarely the result of bad software. They are almost always process failures caused by unclear scope, missing evidence expectations, and weak accountability. To protect your enterprise valuation and ensure M&A readiness, move from reactive searching to an investor-grade diligence process.
Define Your Selection Prerequisites
Before interviewing vendors, establish your target frameworks, your audit timeline, and every system in scope. This prevents providers from setting a generic agenda that ignores your specific technical authority gap.
The Execution Scorecard
Run every candidate for IT compliance services through this four-step validation:
1. Define pass/fail requirements. Mandate specific framework coverage, SRM requirements, and reporting deliverables including evidence outputs.
2. Weight the criteria. Use these benchmarks to compare firms: SRM (20%), deliverables (20%), integrations (15%), operating model (15%), pricing/TCO (15%), and audit support (15%).
3. Conduct two specific calls. Run a technical deep-dive followed by an executive readout. Ensure the vendor can explain technical risk to non-technical stakeholders to verify they can support board-level reporting.
4. Request artifacts. Inspect a redacted report pack, sample SRM, onboarding plan, and sample SOW before signing to ensure their delivery matches the sales pitch.
Surface-the-Truth Questions
Ask these questions to identify hidden operational risks:
- What are the exact boundaries of your assessment?
- Who owns the licenses for compliance automation tools?
- How do you handle auditor coordination and incident escalation?
- What tasks do you explicitly not perform?
Schedule an Audit-Ready Scope Review
Map your technical stack against your framework requirements. Ensure your IT compliance services are built for an exit, not just a monthly check-box.
FAQ
Managed services replace the traditional last-minute scramble before an audit with continuous monitoring and automated evidence generation. By standardizing critical controls like multi-factor authentication, patching, and logging, a provider creates a persistent, documented trail of security hygiene. This proactive approach uses specialized reporting to make exceptions visible immediately. This allows your team to remediate gaps before they transform into audit failures, security incidents, or liability risks that stall business growth.
No. Managed IT compliance services operate based on a Shared Responsibility Model where the provider manages technical controls and produces evidence, but governance remains an internal function. Your internal leadership still owns risk acceptance, policy approval, and business-level decisions. While the provider bridges the Technical Authority Gap by handling the heavy lifting of execution, your internal owner remains responsible for the final oversight of the compliance program. See Section 1 above for the full breakdown of this relationship.
Most modern auditors accept automated evidence provided it demonstrates clear provenance, accurate timestamps, and sufficient context. However, automation is rarely a total replacement for human review. To ensure full acceptance, you should align with your auditor early in the engagement. The most effective strategy combines automated data capture with a human-reviewed narrative to ensure the context behind the data is clear, which satisfies both technical requirements and qualitative audit standards.
The inclusion of these services varies by contract and provider. Many firms distinguish between audit support, such as packaging evidence and participating in walkthroughs, and remediation, which involves the actual engineering changes required to fix identified gaps. It is critical to define what is covered in your monthly retainer versus what is billed as a separate project. Clarifying these boundaries in the Statement of Work protects your EBITDA and prevents budget shock during active audit cycles.
Whether a provider needs certification depends on the defined boundary of your assessment and whether their systems handle, store, or transmit Controlled Unclassified Information (CUI). If the provider’s tools or staff have access to your CUI environment, they may fall within your compliance scope. We strongly recommend documenting a formal scope and Shared Responsibility Model with a CMMC specialist to interpret specific contract-level obligations and ensure your defense supply chain eligibility remains intact. This structured, outcome-focused approach reflects how NUOPTIMA approaches long-term growth and accountability.



