When an SMB leader searches for IT support for small business, they are usually navigating a crisis. Whether facing a security breach or growth-related downtime, these prospects require immediate clarity. NUOPTIMA treats marketing as a compounding revenue asset through a strict RevOps lens. This blueprint provides eight content blocks that improve rankings and increase booked calls by removing buyer friction. Start with the core page structure then layer pricing, SLA, security, and proof.
1. Define Service Depth to Build Immediate Authority
Most pages for IT support for small business capture traffic but fail to convert because they lack concrete specifics. Vague 24/7 promises do not build trust; transparent service depth does. To secure high-intent leads, map technical features directly to buyer outcomes like uptime, security, and profitability.
Use a service depth block to detail the offer:
- Help Desk & Device Management: Eliminates recurring tickets and accelerates onboarding/offboarding.
- Network Monitoring: Minimizes costly downtime through proactive threat detection and resolution.
- Cloud, M365 & Azure/AWS Admin: Ensures data security, compliance, and seamless hybrid scalability.
- Vendor Management: Acts as a single point of contact for all third-party technology providers.
- Who this is for: Hybrid teams (5 to 50 seats) in regulated niches like finance or healthcare.
- Who it is not for: DIY one-person shops.
2. Implement Transparent Pricing Tiers to Qualify High-Intent Leads
Hidden rates fill your calendar with unqualified leads. Pricing opacity kills conversions because professional buyers must verify budget alignment before committing to a discovery call. Transparent ranges qualify prospects instantly and protect your margins without rigid quotes.
Tier your IT support for small business offer in plain English:
- Basic Monitoring: $75 to $125 per user/month for foundational maintenance.
- Standard Managed IT: $125 to $200 per user/month including priority SLAs and strategic roadmap reporting.
- Advanced/Compliance: $200 to $300+ per user/month for firms needing intensive security stacks and regulatory audits.
Define scope boundaries to prevent bad-fit leads and protect profitability. Explicitly exclude onboarding fees, project work, after-hours rules, on-site add-ons, and hardware procurement markups from the base monthly price.
3. Build Trust with a Transparent SLA Framework
Small business owners often fear the ticket black hole when outsourcing IT support for small business. Eliminate this friction by publishing a concrete Service Level Agreement (SLA) that defines measurable response and resolution commitments. This transparency differentiates your firm and signals that support is a data-driven asset rather than a mystery.
Use a severity matrix to set clear expectations:
- P1 (Critical): 30 to 60 minute response for total outages.
- P2 (High): 2 to 4 hour response for degraded performance.
- P3 (Medium): 4 to 8 hour response for workstation issues.
- P4 (Low): 1 business day for general requests.
Differentiate between initial response and full resolution to manage expectations. Include operational specifics like business hours and escalation paths to prevent disputes and build investor-grade operational equity.
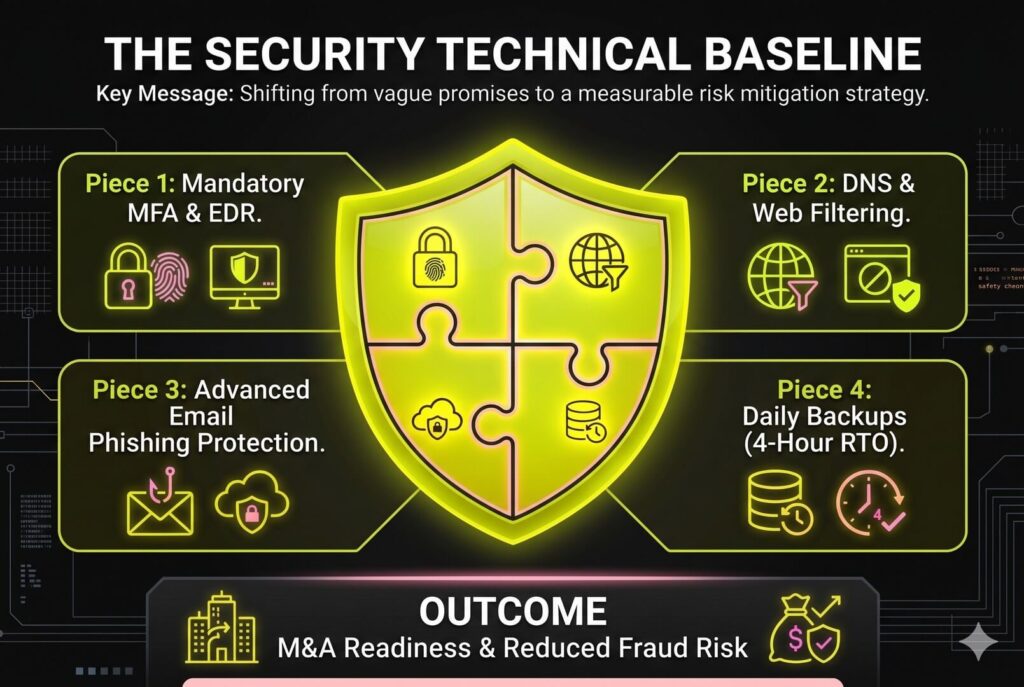
4. Codify a Security Baseline to Outshine Vague Competitors
Competitors often sell security through vague promises that fail to address founder anxieties. To capture high-intent leads for IT support for small business, replace ambiguity with a transparent technical baseline. This shifts the dialogue from a nebulous safety net to a measurable risk mitigation strategy that builds investor-grade equity and M&A readiness.
Your baseline must include:
- Mandatory MFA and Endpoint Detection and Response (EDR).
- Automated patching and DNS/web filtering.
- Advanced email security to block phishing at the perimeter.
Data protection requires more than storage. Specify daily backups with 24-hour testing and a four-hour Recovery Time Objective (RTO). By linking these controls to business outcomes like reduced fraud risk and audit readiness, you establish technical authority before the first sales call.
5. Build Vertical Landing Pages to Dominate Compliance-Heavy Niches
Generic marketing for IT support for small business leads to low-margin price wars by ignoring regulatory risks. Build vertical landing pages for niches like medical (HIPAA), retail (PCI), or legal firms to capture high-intent traffic. These pages transform your MSP from a commodity vendor into a specialized strategic asset.
Showcase industry-grade proof points to validate technical authority:
- Compliance Processes: Detail workflows for access control, immutable logging, and vendor management.
- Vertical Tech Stacks: List supported platforms like EMR, legal practice management, or POS software.
- Service Scope: Define what we do vs. don’t regarding technical controls to focus on audit readiness without making legal claims.
Aligning with a buyer’s specific risk profile justifies premium pricing and accelerates revenue outcomes.
6. Define On-Site Boundaries to Prevent Operational Churn
Hardware outages like failed switches or POS terminal crashes cannot be resolved via Zoom. While remote IT support for small business handles cloud applications and software endpoints, physical infrastructure requires local intervention. Defining your physical reach early prevents operational churn and qualifies leads based on your real-world capacity.
If you offer hybrid support, explicitly state your service area radius and response windows. For example, a four-hour arrival guarantee within 30 miles of your office sets clear expectations for critical hardware failures. Build service-area pages for specific regions to capture high-intent local search traffic. These pages confirm you provide the physical presence needed for on-prem gear, distinguishing your firm from purely remote competitors.

7. Codify Responsibility to Eliminate Vendor Blame
SMBs often get trapped in vendor finger-pointing where software providers, hardware vendors, and MSPs deflect blame for downtime. You can eliminate this friction with a Shared Responsibility Matrix (SRM). Written in plain English, this document defines whether the MSP owns, the client owns, or both share responsibility for:
- Patching and backups
- Admin credentials
- Vendor ticket management
- Security tooling
This transparency signals operational maturity and de-risks the partnership by closing the Technical Authority Gap. Supplement the SRM with a hardware procurement block to standardize laptop provisioning, lifecycle tracking, and warranty handling for servers and network equipment. Maintaining on-site spare devices ensures rapid replacement and prevents productivity loss. Professional IT support for small business relies on these lifecycle standards to stop technical debt from causing system failures.
FAQ
Monthly costs for managed IT typically fall into three tiers. Basic monitoring ranges from $75 to $125 per user, while standard support with strategic roadmapping costs $125 to $200 per user. Advanced compliance-heavy support often exceeds $200 per user. Factors like security complexity and SLA response times drive these rates. Common extras to budget for include one-time onboarding fees, project-based hardware deployments, and after-hours on-site emergency visits.
Managed IT services are generally superior for businesses seeking growth and stability. Unlike the reactive break-fix model, which leads to volatile costs and prolonged downtime, managed services provide proactive monitoring and predictable monthly billing. Break-fix may suffice for very small operations with low technical dependency, but most SMBs require the uptime guarantees and security maturity that only a managed model provides. See Define Service Depth above for more details.
Remote support is sufficient for cloud applications and software troubleshooting, but physical locations often require a hybrid approach. If your business relies on local servers, network switches, or point-of-sale systems, you need a provider capable of on-site intervention. When evaluating remote-first providers, negotiate a specific on-site response SLA for critical hardware failures. This ensures that physical infrastructure issues do not lead to multi-day outages.
A professional security baseline must include multi-factor authentication, endpoint detection and response, and automated patching. Email security and encrypted backups with regular recovery testing are also non-negotiable. Your choice of provider should be driven by their ability to meet specific Recovery Time Objectives and Recovery Point Objectives. These controls move your business beyond basic safety and toward true audit readiness. See Codify a Security Baseline for the full technical list.
Avoid providers that offer vague Service Level Agreements or fail to provide a Shared Responsibility Matrix. Other red flags include a lack of regular reporting, missing client references, or unclear offboarding procedures. A transparent partner should treat your IT as a revenue asset rather than a hidden cost center. To see what your current site and offer are missing, request a Competitor Intent Report or an M&A Readiness Audit-style assessment today.



