Technical excellence is the baseline, yet most firms struggle with a pipeline that lives or dies on referrals. A sustainable cybersecurity lead generation strategy requires a system rather than a single channel. We transform technical authority into qualified, sales-ready demand by combining high-intent SEO and Generative Engine Optimization (GEO) with RevOps instrumentation. NUOPTIMA provides AI-first SEO and RevOps to accelerate MSP and MSSP growth. Start with intent capture, then build trust, then engineer conversion.
1. Capture Bottom-Funnel Intent with SEO and GEO
Many cybersecurity firms struggle with a Technical Authority Gap where high traffic fails to yield SQLs. Ranking for what is malware attracts students, not CISOs. To build a predictable cybersecurity lead generation strategy, stop chasing broad volume and target crisis moments where budget is already active.
Capture buyers during high-stakes scenarios:
- Looming NIS2 or CMMC compliance deadlines.
- Cyber insurance renewal rejections.
- Post-breach recovery or audit failures.
Shift focus from definitions to action-oriented keyword clusters. Instead of MDR, target MDR for healthcare compliance or ransomware incident response retainer. Every core service requires a money page with industry-specific schema, certifications, and outcome-based proof to convert high-intent visitors.
To dominate the next era of search, implement a Generative Engine Optimization (GEO) layer. Publish citation-worthy frameworks and checklists that LLMs like Perplexity and ChatGPT can quote. This ensures your brand is the primary recommendation when a decision-maker asks an AI for the best MSSP in their vertical.
Measure success by the percentage of organic leads matching your ICP and the resulting SQL rate. To identify your current authority gaps in both Google and AI search, [book an SEO/GEO audit with NUOPTIMA.
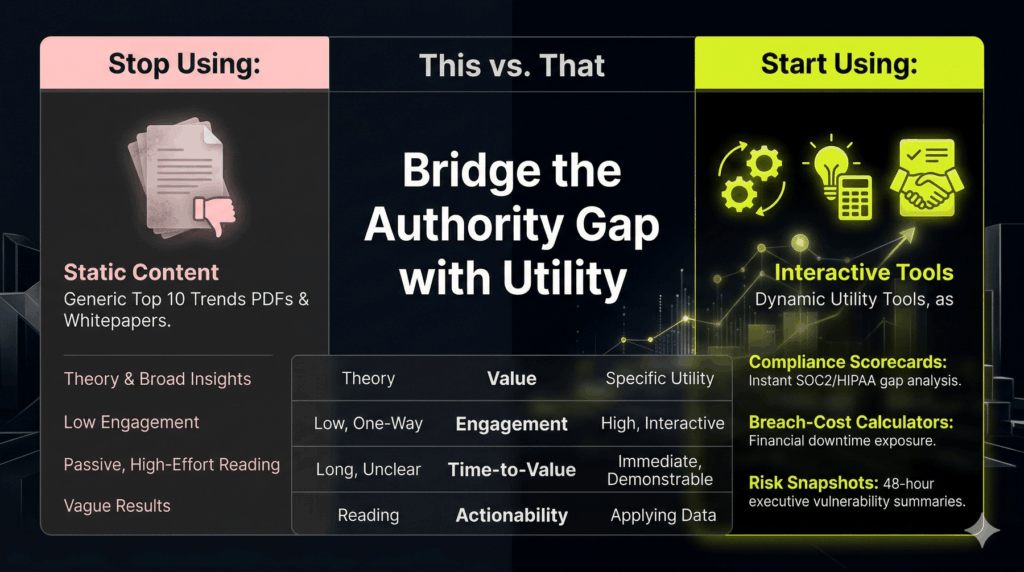
2. Replace Fluffy Lead Magnets with High-Utility Micro-Tools
Generic whitepapers produce high lead volume but zero pipeline. Cybersecurity buyers, from CISOs to technical founders, ignore marketing fluff like Top 10 Trends PDFs. They prioritize tools that solve immediate professional anxieties, such as audit failures or miscalculated risk. Replacing passive content with active micro-tools bridges the Technical Authority Gap and captures high-intent prospects before they engage competitors.
Deploying targeted tools qualifies interest at the point of entry:
- Compliance Scorecards: Provide SOC 2, HIPAA, or NIS2 readiness checklists with instant gap analysis.
- Breach-Cost Calculators: Frame downtime and insurance exposure in board-ready financial terms to justify security spend.
- Risk Snapshots: Deliver a 48-hour executive risk snapshot with a board-ready summary of critical vulnerabilities.
This pivot transforms your cybersecurity lead generation strategy into an SQL engine. Embed these tools within high-intent SEO pages and promote them via LinkedIn role-targeted ads. Use retargeting pixels to re-engage site visitors who exit before converting.
Maintain lead quality by designing intake forms with three to five strategic qualification fields. Capture the prospect’s current tool stack, industry, and implementation timeline to ensure every lead is sales-ready.
3. Treat Trust Signals as Conversion Infrastructure
Cybersecurity lead generation strategies often fail due to unspoken friction. If a landing page feels generic, it widens the Technical Authority Gap, causing high-intent buyers to ghost CTAs. Treat trust signals as conversion infrastructure rather than branding fluff to answer the reader’s primary question: Is this vendor safe to talk to?
Deploy a Trust Stack directly next to lead forms to reduce friction and improve engagement:
- Evidence: Case studies showing measurable ROI or risk reduction, anonymized to protect client confidentiality.
- Competence: Clear display of certifications like SOC2, CISSP, or specific partner badges.
- Process: A What Happens After You Book block that demystifies the onboarding experience and the first 30 days.
- Safety: Use minimal-data intake forms and highlight your responsible disclosure stance to signal a high safety posture.
- Social Proof: Peer reviews and client logos to validate market presence and authority.
Position these signals above the fold on money pages and adjacent to your primary CTA. This layout targets the silent anxiety that prevents technical founders and CISOs from engaging. Monitor landing page conversion rates and demo show rates by offer to quantify the impact of visible trust. Systematic transparency transforms a skeptical visitor into a qualified discovery call.
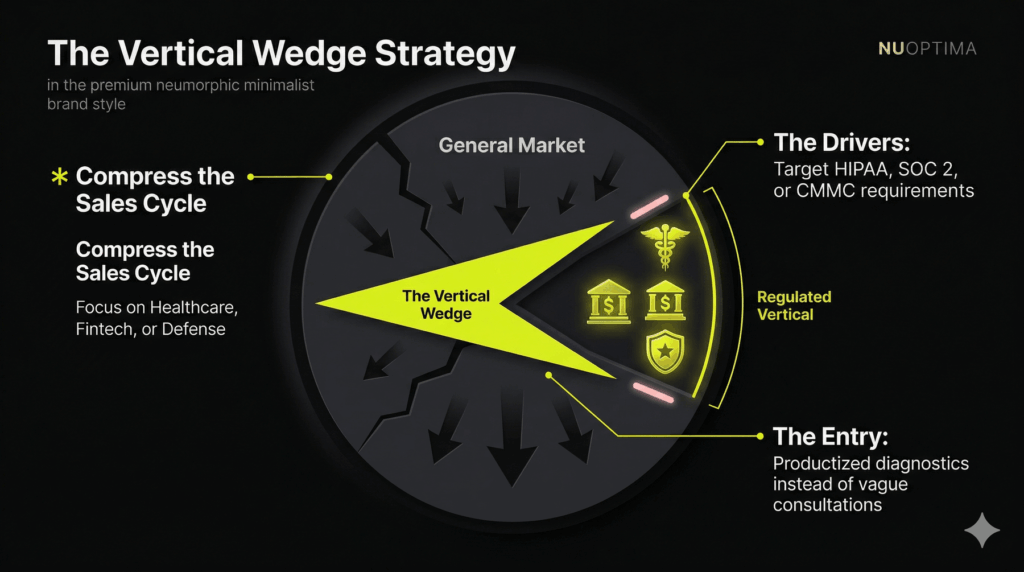
4. Narrow Your Vertical Focus to Compress Sales Cycles
Generalist positioning invites price comparison against commodity providers. Security buyers prioritize specialists who understand their specific regulatory constraints. To compress sales cycles and eliminate the Technical Authority Gap, you must transition to a narrow ICP. Define your target in strict operational terms:
- Industry vertical (e.g., Healthcare, Fintech, or Defense)
- Compliance drivers like HIPAA, SOC 2, or CMMC
- Seat count and deal size floor
- Specific tool stack and buying committee structure
Choosing a vertical wedge allows you to build a moat around regulated pain points that generalists cannot address. Pair this focus with a productized entry offer like a time-boxed diagnostic, readiness assessment, or executive risk snapshot. Avoid vague consultations. These high-intent offers must deliver value to two distinct audiences:
- Practitioners: Detail the technical risk and clear remediation paths.
- Executives/Boards: Quantify business impact, downtime risks, audit exposure, and insurance eligibility.
This precision ensures you are the obviously right choice before the first discovery call. It filters out unqualified leads and positions your firm as a strategic partner rather than a vendor. Measure the success of your cybersecurity lead generation strategy by tracking the SQL rate and average deal size across your vertical-specific pages.
5. Engineer Money Pages to Convert Intent into Meetings
Traffic is not pipeline. A cybersecurity lead generation strategy fails when SEO drives clicks but forms create a CRM graveyard. To convert intent into meetings, design money pages around qualification rather than volume. This transforms inbound demand into investor-grade revenue that increases enterprise valuation.
High-converting pages must define the target ICP and the specific business outcome delivered. Every page requires a concrete offer with clearly defined deliverables:
- Technical pilots or security diagnostics.
- A what happens next timeline to reduce buyer friction.
- Dual CTA paths: Book a Call for active buyers and Request Assessment for research phases.
Use conditional form logic to protect sales calendars. Require fields like seat count or compliance drivers (such as SOC2 or CMMC) only for high-fit prospects. Automate lead routing by vertical or region and enforce a strict speed-to-lead SLA. If a lead is not sales-ready, trigger an automated technical nurture sequence in your CRM to maintain brand authority.
Track performance through speed-to-lead, meeting booked rates, and MQL-to-SQL conversion. These metrics verify that your technical authority is translating into a predictable pipeline. This transition bridges the gap between marketing spend and measurable EBITDA growth.
6. Align Paid and Organic Social to High-Intent Security Roles
Most MSPs treat LinkedIn as a billboard for generic thought leadership. Technical decision-makers buy solutions to specific regulatory or operational fires, not awareness. Stop wasting ad spend on broad interests. Match specific security offers to specific roles to bridge the Technical Authority Gap.
Effective campaign design targets CISOs, IT Heads, or Compliance leads by industry and company size. Replace generic whitepapers with high-utility vertical checklists, readiness scorecards, or executive summary diagnostics. Creative must address specific triggers like audit deadlines or vendor risk assessments without relying on pure FUD.
Reinforce paid efforts with weekly organic proof posts. Share mini case study teardowns or checklist excerpts to build technical trust before the first call. Use retargeting pixels to warm up website visitors with assets before serving a book assessment call to action.
Track performance via CPL by segment, cost per meeting, and SQL rate. This precision ensures your cybersecurity lead generation strategy creates investor-grade revenue data. Granular targeting moves the firm from renting traffic to owning the primary conversation in a specific vertical.
7. Leverage Communities and Partnerships as Measurable Pipeline Channels
SEO and ads often fail to convert because cybersecurity buyers decide privately. High-intent prospects validate vendors in CISO peer groups, MSP communities, and compliance circles like ISACA or SOC2 forums. This dark social layer is where you bridge the Technical Authority Gap. Transition from passive observer to active enabler to capture this demand.
Deploy a strategy centered on technical enablement rather than generic pitches. Position your firm as an authoritative peer by contributing high-utility assets to these communities. Focus on:
- SOC2 and CMMC audit templates
- Ransomware incident response checklists
- Detailed technical teardowns of recent breaches
Simultaneously, build partnership plays with adjacent trusted firms like cloud integrators, compliance consultants, and MSPs without security arms. These allies provide the warm entry points cold outreach often lacks. Measure these channels with the same rigor as performance advertising by using:
- Self-reported attribution (How Did You Hear About Us? fields)
- Partner-specific landing pages for full-funnel CRM tracking
- Co-branded diagnostic tools or joint webinars
This approach turns unmeasurable peer trust into predictable revenue and investor-grade pipeline data, directly increasing your firm’s enterprise valuation. This ensures your cybersecurity lead generation strategy captures the entire buyer journey.
8. Use Account-Based Experience (ABX) to Navigate Multi-Stakeholder Deals
Cybersecurity deals stall when the buying committee lacks a unified path to yes. While practitioners seek technical validation, executives require risk mitigation and financial justification. If your funnel ignores either, you fail to bridge the Technical Authority Gap and risk terminal deal stagnation.
An ABX-driven cybersecurity lead generation strategy transforms anonymous interest into a guided journey based on high-intent signals. Act immediately on triggers such as:
- Repeat visits to high-value service pages or technical tool usage.
- Engagement with specific compliance frameworks or whitepapers.
- Market triggers like new funding rounds, key job postings, or regulatory shifts.
Design distinct experiences to educate both stakeholders simultaneously:
- Practitioners: Provide architecture overviews, threat model approaches, and process diagrams.
- Executives: Deliver board-ready risk framing, ROI projections, and clear implementation roadmaps.
Execute a multi-channel retargeting sequence that transitions from social proof to a diagnostic offer, followed by a vertical-specific case study and a direct book CTA. Support this with short, role-specific email nurtures that prioritize technical authority over generic marketing FUD.
Track re-engagement rates and opportunity creation from nurtured accounts. This approach ensures your pipeline produces the investor-grade data required for M&A readiness and sustainable, high-valuation growth.
9. Connect Marketing to EBITDA with Strategic RevOps
Cybersecurity lead generation strategies often fail at attribution, leaving leaders with vanity metrics instead of investor-ready data. RevOps transforms marketing into a repeatable asset by linking spend directly to EBITDA and enterprise value. This control system prevents the CEO and sales team from viewing inbound leads as random events and builds the organic equity needed for a successful exit.
To eliminate guesswork, implement this minimum viable RevOps setup:
- Lifecycle Stages: Define Lead – MQL – SQL – Opp – Won with entry and exit criteria to ensure sales and marketing alignment.
- Lead Scoring: Weigh firmographics against intent signals like pricing page visits, whitepaper downloads, or technical tool usage.
- Enforced SLAs: Map response times and follow-up cadences to scores to capture prospects during high-intent crisis moments.
Attribution must track source, medium, offer, and landing page to report pipeline by channel and vertical. Maintain a weekly pipeline review and monthly conversion diagnostics to ensure the engine remains defensible during M&A due diligence. This rigor turns your GTM strategy into a valuation multiplier rather than a collection of unlinked experiments.
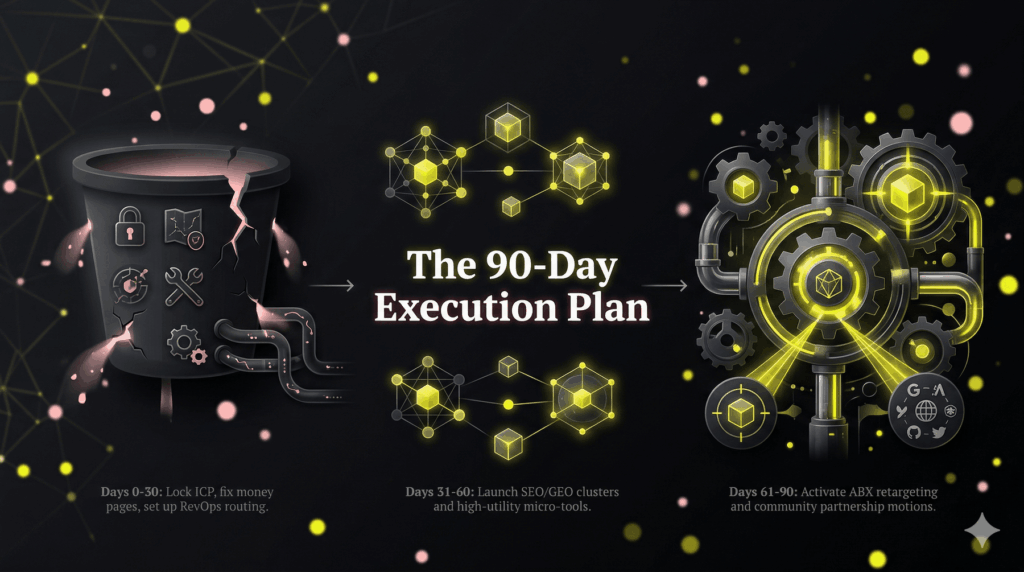
Execution Plan: A 90-Day Cybersecurity Lead Generation Strategy
Cybersecurity lead generation strategy success requires precise sequencing. Launching high-spend ads before establishing trust or scaling SEO before fixing conversion paths creates a leaky revenue bucket. Use this 90-day execution plan to align technical authority with market intent and build an investor-grade revenue engine.
Days 0 to 30: Establish the Technical Foundation
The first month prepares your infrastructure for high-intent traffic. Avoid rushing into paid spend until these operational pillars are active.
- Lock ICP and Vertical Wedge. Select one compliance-heavy vertical such as Fintech, Healthcare, or Defense. Focus on sectors where you possess proven technical authority and high lifetime contract value.
- Define a Productized Entry Offer. Replace vague consultations with a time-boxed diagnostic or micro-tool. Create specific offers like a CMMC Gap Analysis or 48-Hour Risk Snapshot to provide immediate value.
- Fix Money Pages and Routing. Re-engineer service pages to include a dual CTA path. Provide one clear path for active buyers and another for research-phase prospects to capture all intent levels.
- Stand Up RevOps Basics. Configure your CRM with clear lifecycle stages and automated routing. Enforce strict speed-to-lead SLAs to ensure sales teams handle high-intent inquiries immediately.
Outcome: You will have a high-converting home base and a validated target profile ready for traffic.
Days 31 to 60: Capture Intent and Establish Authority
Shift your focus to capturing active demand through search and distributing authority to specific technical roles.
- Publish SEO and GEO Clusters. Build action-oriented content clusters around industry crisis moments. Ensure content is citation-heavy to secure AI search recommendations and dominate Generative Engine Optimization.
- Deploy a High-Utility Micro-Tool. Embed a breach-cost calculator or compliance scorecard on primary money pages. This captures leads that typically ignore standard whitepapers or PDFs.
- Create Proof Assets. Publish one deep-dive case study and a What Happens Next process overview. This transparency targets the technical anxiety that often prevents CISOs from booking calls.
- Launch LinkedIn Distribution. Use role-based targeting to drive technical decision-makers directly to your diagnostic offer or micro-tool.
Outcome: You will see high-intent organic and paid traffic entering a validated conversion path.
Days 61 to 90: Scale and Compound Growth
Scale successful channels and optimize the feedback loop between marketing data and sales outcomes.
- Activate Retargeting and Role-Based Nurture. Implement ABX principles to re-engage accounts that interacted with your tools but did not book a call. Provide role-specific technical proof to these prospects.
- Start Community and Partner Motions. Launch repeatable co-marketing offers with non-competing partners like cloud integrators or compliance consultants to expand your reach.
- Review Funnel Metrics and Iterate. Use RevOps data to identify which vertical-specific pages yield the highest SQL rate. Double down on high-performing clusters and prune underperforming ad spend.
Outcome: You will possess a measurable, investor-ready system that builds organic equity and increases enterprise value.
FAQ
SEO and GEO typically show initial momentum within three to six months. While building broad domain authority takes time, focusing on bottom-funnel money pages and niche compliance keywords can trigger high-intent leads much sooner. Optimizing your conversion infrastructure can also produce an immediate lift in lead volume from existing traffic before rankings even shift. For a detailed timeline, see the Execution Plan section above.
Educational content should remain ungated to build technical authority and earn AI search citations. However, you should gate high-utility tools like compliance calculators or risk assessments that provide personalized outputs. This approach uses progressive capture to build trust first, making prospects more willing to share details once the value is proven. Refer to the section on High-Utility Micro-Tools for specific examples.
Avoid Fear, Uncertainty, and Doubt (FUD) by using value-first framing. Instead of highlighting impending doom, focus on business resilience, readiness, and positive compliance outcomes. Use objective proof like executive risk snapshots and process diagrams to demonstrate competence. Urgency is naturally created when you show a clear path from current vulnerability to a secure, compliant state without relying on scare tactics.
Focus on revenue-aligned metrics rather than vanity traffic. The most critical KPIs include ICP-fit rate, MQL to SQL conversion, cost per booked meeting, and total sales cycle length. Track these within a robust RevOps framework to ensure marketing spend directly impacts EBITDA. Current industry benchmarks suggest a target MQL to SQL rate of 25% to 35% for high-intent cybersecurity leads.
Implement a two-track content strategy that addresses the technical requirements of practitioners and the financial risks of executives. Use a single routed call to action, such as a security diagnostic, then apply role-based follow-up sequences in your CRM. This alignment is maintained through a strict RevOps SLA that ensures every lead is nurtured with the specific technical or business data they need.



