Cybersecurity leaders often face the Technical Authority Gap. You possess superior capabilities, yet skeptical CISOs don’t trust the message. Conventional marketing fails by prioritizing vanity traffic over compliance fluency and technical depth. To build organic equity, you need a cybersecurity marketing agency that delivers investor-grade pipeline and measurable revenue outcomes. This guide provides 10 essential criteria to evaluate partners alongside a strategic 90-day selection process to ensure your marketing drives actual M&A readiness.
1. Demand Technical Fidelity Over Marketing Hallucinations
Most agencies dumb down security concepts until they lose credibility with cynical CISOs. If your content feels like a generic AI prompt, you are not building authority. You are creating technical debt. Technical fidelity is the primary differentiator for a high-growth cybersecurity marketing agency.
Elite partners use a Subject Matter Expert (SME) model where named practitioners review technical collateral. Content must withstand the scrutiny of a security lead who spots technical hallucinations instantly. This correctly translates technical reality into buyer-ready positioning, bridging the Technical Authority Gap and increasing enterprise valuation.
To verify technical depth in 20 minutes, request these specific samples:
- Threat-informed narratives.
- Incident-response explainers.
- SOC reporting workflows and technical review cycles.
Inquire about reference frameworks like NIST-style controls or MITRE threat narratives. Red flags include vague writer pools, lack of SME review, or an inability to explain internal accuracy controls. This prevents hiring security-flavored generalists who damage brand trust, create sales friction, and stall revenue outcomes.
2. Engineer a Baseline Trust Stack to Neutralize Buyer Risk
In cybersecurity, trust is the product. Even the most sophisticated SOC fails if a skeptical CISO cannot verify your track record in seconds. A specialized cybersecurity marketing agency must architect a baseline trust stack that reduces perceived risk for high-intent buyers while bridging the Technical Authority Gap.
This baseline stack includes:
- Case studies with recognizable logos, performance numbers, and what changed narratives.
- Buyer-role testimonials that address specific pain points of technical decision-makers.
- Earned media, PR strategy, and analyst mentions to validate market position.
- Consistent executive presence that projects authority over generic social noise.
Operationalizing trust requires tangible proof that neutralizes the vendor skepticism tax. Ask potential partners to demonstrate before and after proof assets and explain how they influenced meeting volume or close rates.
A significant red flag is any agency focusing exclusively on top-funnel metrics like impressions. Without specific sales enablement outputs, you fail to build the organic equity and M&A readiness required for long-term valuation.

3. Focus on Revenue Operations (RevOps) and Pipeline Attribution
If an agency delivers 500 leads but zero closed deals, you bought a spreadsheet, not growth. A cybersecurity marketing agency acting as a true partner functions as a fractional RevOps department. They must engineer CRM hygiene, lead scoring, and lifecycle stages to match your specific sales velocity and technical authority.
Demand the following to ensure investor-grade reporting:
- Definitions of MQLs and SQLs that match your actual sales reality.
- Pipeline attribution categorized by channel and vertical segment.
- A weekly funnel view that tracks revenue velocity instead of distracting monthly traffic reports.
A strategic partner traces the journey from a technical page visit to an opportunity created in the CRM. They eliminate busy marketing and the technical authority gap by forcing revenue outcomes.
Ask potential agencies these qualifying questions:
- How do you track the path from keyword or page to meeting booked and opportunity created?
- What is your plan to reduce CAC and increase the SQL rate rather than just increasing lead volume?
4. Bridge Technical Precision with High-Intent Content Clusters
Generalist agencies often treat SEO and content as isolated buckets, leaving critical MDR or SOC service pages to gather digital dust. Technical SEO is the structural foundation that prevents lost demand and builds organic equity. Your site architecture must include:
- Mapping for service lines including MDR, SOC, vCISO, and GRC
- Advanced crawl control and schema markup
- Clean analytics for investor-ready attribution
Content must bridge the Technical Authority Gap by mapping directly to the buying journey. Build authority clusters that guide prospects from initial problem identification through vendor evaluation and final selection. Strategic internal linking must connect technical explainers to conversion-focused pages, ensuring a seamless experience for both search crawlers and skeptical CISOs.
Challenge your cybersecurity marketing agency by asking: Show your technical SEO audit template and three fixes that shifted lead volume, not just vanity rankings. If they cannot link technical site health to revenue outcomes, they are not preparing your firm for an investor-grade exit.
5. Capture the AI-First Buyer via Generative Engine Optimization (GEO)
Ranking on Page 1 is no longer enough if you are missing from the AI summary. Modern security buyers increasingly use LLMs like Perplexity and SearchGPT to shortlist technical partners. If your cybersecurity marketing agency focuses only on traditional blue links, you risk invisibility exactly where critical research starts.
Answer engine optimization requires shifting from keyword density toward entity strength and high-confidence references. Look for an agency with a repeatable method for:
- Entity mapping to solidify your brand’s technical authority.
- Structured FAQ assets that AI models prioritize for summaries.
- Expert-led content designed specifically to earn citations as a primary source.
These signals transform your technical expertise into high-signal data points for LLM consumption. Ask prospective partners how they measure visibility in answer engines and which technical assets they build first to earn citations. A major red flag is a cybersecurity marketing agency treating GEO as a buzzword without a specific measurement plan. Without verifiable tracking, your brand remains a ghost in the interfaces buyers use to validate your technical authority.
6. Verify Competency in Service Packaging vs. Product Marketing
SaaS-focused agencies often fail when scaling MSPs because they mistake service delivery for product features. While products sell capabilities, services sell trust, outcomes, and the delivery model. An elite cybersecurity marketing agency recognizes you sell an ongoing relationship, not a static tool. This bridges the Technical Authority Gap with high-intent decision-makers.
A strategic partner must package technical expertise into tangible tiers, SLAs, and onboarding frameworks that reduce friction in long-cycle deals. They should help you pivot from commoditized per-seat pricing to value-based narratives focused on compliance outcomes and risk mitigation. This shift justifies premium margins, prevents discounting, and builds the organic equity required for investor-grade scrutiny and maximized enterprise value.
Question to ask:
Show an example of how you repositioned a client from per-device pricing to value-based outcomes.
Red flags:
- One-size-fits-all messaging frameworks that ignore operational nuances.
- Zero guidance on service packaging, SLAs, or tiering.
- Failure to address long-cycle sales narratives inherent in B2B security.
7. Operationalize Compliance as a Value Driver
Regulated industries buy reduced audit pain and lower breach risk. If your marketing promises compliance while your technical team only provides controls, you create immediate friction with audit-weary CISOs. This disconnect stalls the sales cycle when high-intent prospects spot technical inconsistencies. Your cybersecurity marketing agency must bridge this gap by communicating these outcomes accurately and credibly.
Credible compliance marketing translates abstract controls into business value through:
- Vertical-specific landing pages for HIPAA, SOC 2, or CMMC.
- Evidence-friendly claims aligned with framework requirements.
- High-precision GRC content that builds technical authority.
To verify competency, request assets like vCISO playbooks, GRC landing pages, and audit-readiness checklists.
Risk management is critical to prevent overpromising. Ensure your agency uses a formal review process to distinguish marketing narratives from legal advice. A major red flag is any provider offering generic compliance content without documented internal review controls. This strategy builds authority in regulated markets and reduces sales friction by neutralizing compliance objections before they occur.
8. Demand Coordinated Multi-Touch Programs Over Single-Channel Flukes
High-intent search ads often fail because complex cybersecurity contracts are rarely won on a first impression. Buying committees typically require six to eight touches across multiple channels before booking a discovery call. A premier cybersecurity marketing agency must execute a minimum viable multi-channel strategy to bridge the technical authority gap.
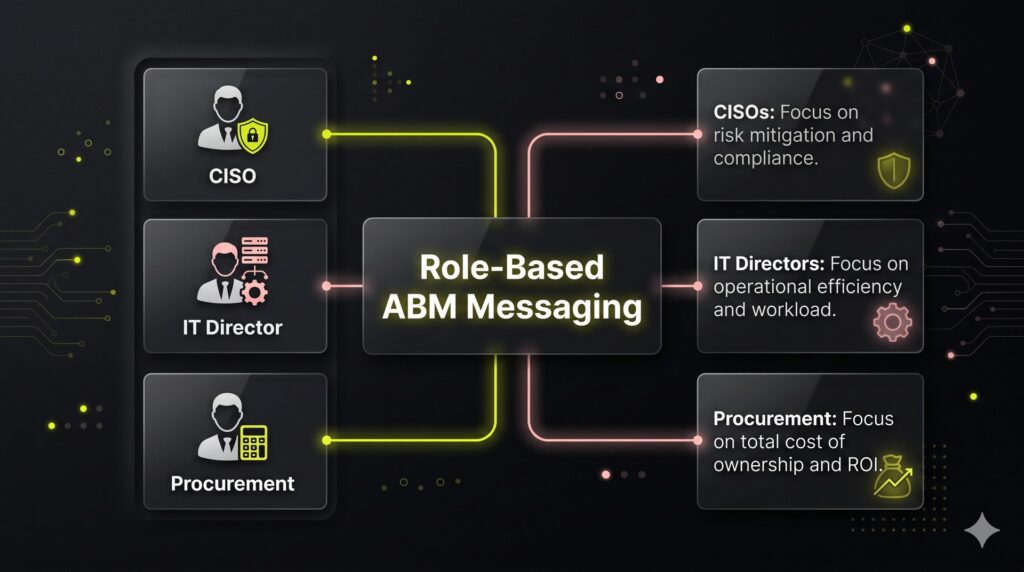
This involves an ABM target list supported by role-based messaging:
- CISOs: Focus on risk mitigation and compliance.
- IT Directors: Focus on operational efficiency and workload.
- Procurement: Focus on total cost of ownership and ROI.
Reinforce these narratives through retargeting that serves educational technical assets instead of repetitive demo requests. Success is measured by meeting rates, opportunity creation, and target account engagement rather than vanity impressions.
When interviewing agencies, ask: How do you align content, paid, and outbound so the story remains consistent across touchpoints? A major red flag is any paid-only proposal that lacks a clear conversion path or a dedicated sales enablement layer. This approach builds asset-based organic equity and sustained demand instead of volatile spikes of low-intent leads.
9. Prioritize Partner Enablement Muscles Over Direct Demand Gen
If your growth strategy relies on a partner ecosystem, hiring an agency focused solely on direct demand generation is a strategic error. Channel partners require specialized infrastructure to sell your expertise effectively rather than just passing leads. High-value enablement includes:
- Streamlined partner onboarding.
- Campaign-in-a-box assets.
- Co-brandable landing pages.
- Technical sales enablement battlecards.
To verify an agency’s maturity, ask for a functional partner kit example. A qualified cybersecurity marketing agency must explain how they manage Marketing Development Funds (MDF) and co-op allocation. They should also demonstrate how they track partner-sourced pipeline within your CRM to ensure every deal has clear attribution.
Avoid providers that claim channel expertise but lack formalized MDF processes or partner adoption metrics. Red flags include the absence of a co-branding workflow or evidence of active partner engagement. Effective agencies treat enablement as a core revenue engine that improves partner time-to-first-sale. This ensures your technical authority scales across every third-party touchpoint.
10. Audit for Conversion Readiness to Stop Wasting High-Intent Traffic
High-intent traffic is wasted if buyers cannot verify your credibility instantly. A conversion-ready site prioritizes technical proof above the fold, replacing generic imagery with ICP-specific value propositions. Focus on low-friction entry points:
- Rapid security assessments
- Compliance gap audits
- Direct Book a Call calendars
Your cybersecurity marketing agency must relentlessly test landing page offers and form field efficiency. Critical elements for skeptical CISOs include pricing clarity, SOC2 certifications, and vertical-specific case studies. Continuous optimization of CTAs and trust signals reduces sales friction while establishing technical authority. This transforms your website into a scalable revenue machine rather than a static digital brochure.
When vetting partners, ask: What are your first three CRO tests in month one, and how do you decide winners? An expert partner defines success by SQL volume and pipeline impact, not just superficial clicks. This data-driven approach stops pipeline leakage and builds the organic equity necessary for an investor-grade valuation.
How to Hire a Cybersecurity Marketing Agency: The 90-Day Execution Roadmap
Treat the selection of a cybersecurity marketing agency as a rigorous procurement process rather than a creative exercise. This structured approach eliminates the Technical Authority Gap and builds investor-ready organic equity. Follow this four-step plan to de-risk your decision and align your growth engine with your exit strategy.
Step 1: Build a One-Page Scorecard Before Taking Calls
Evaluate every agency against technical pillars instead of aesthetic slide decks. Build a scorecard with specific evaluation columns: technical depth, compliance fluency (SOC2/HIPAA), SEO/GEO capability, RevOps/attribution maturity, channel experience, proof assets, CRO focus, and communication cadence.
Define your North Star metric as Sales Qualified Leads (SQLs) and pipeline value. Include leading indicators such as meetings booked and opportunity creation rates. This ensures the agency understands that success is measured by revenue outcomes, not just traffic volume.
Step 2: Require Verifiable Evidence Over Sales Promises
Force specificity during the sales process to separate operators from generalists. Ask for two relevant cybersecurity case studies and two technical content samples that demonstrate a clear subject matter expert (SME) workflow. Demand to see a sample reporting dashboard and a draft 90-day execution plan. Ask the pivotal question: What exactly will you ship in the first 30 days? You will see immediately if the agency possesses a repeatable delivery framework or is relying on vague monthly retainers.
Step 3: Run a Paid Pilot (30 to 60 Days)
Execute a 30 to 60-day paid pilot with clear, non-negotiable deliverables. Use this phase to complete technical SEO fixes, build one high-intent conversion landing page, create three bottom-funnel content pages, and perform a CRM stage cleanup with a reporting setup. Establish pass/fail criteria upfront. Success requires that baseline tracking is operational, a measurable conversion lift occurs, and the quality of booked meetings aligns with your technical ICP.
Step 4: Lock the Operating Model
Establish a strict operating rhythm to maintain momentum. Schedule a weekly pipeline review and a monthly strategic session to align stakeholders. Assign a single owner to manage both marketing and RevOps to prevent data silos. This structure ensures every marketing dollar contributes to your long-term valuation and M&A readiness.
If you want a pipeline-first, security-native partner to build your technical authority and bridge the gap to enterprise-grade growth, explore the NUOPTIMA framework at nuoptima.com.
Frequently Asked Questions
FAQ
Typical monthly retainers fall into three primary bands. Entry level foundational programs usually start between $5,000 and $8,000 for basic SEO and content. Growth tier retainers range from $10,000 to $20,000 and include fractional RevOps and paid media management. Enterprise engagements often exceed $25,000 for full funnel dominance. Always compare proposals based on pipeline KPIs and specific deliverables. Hours are a vanity metric that hides inefficiency while technical outputs drive real enterprise valuation.
Real results require a structured ramp up. The first 30 days focus on technical SEO audits and measurement setup. You should see early conversion wins between 30 and 60 days by optimizing existing high intent pages and improving conversion paths. Compounding authority through SEO and GEO takes 3 to 9 months to fully mature. This timeline accounts for the long cybersecurity sales cycle and the time needed to establish technical fidelity with search engines and AI models.
Distinguish expertise via three telltales. First, a service native agency focuses on packaging and SLAs rather than product features. Second, their proof assets must highlight outcomes such as improved compliance posture instead of simple software downloads. Third, their RevOps strategy must tie marketing activity directly to sales opportunities in your PSA or CRM. Generalist SaaS agencies often fail to grasp the trust based and relationship driven nature of MSSP growth.
Move beyond generalities by asking for the names of the Subject Matter Experts who review technical copy. Request a sample dashboard to evaluate their reporting maturity and pipeline attribution. Ask to see examples of bottom funnel work, such as technical service explainers or comparison pages. Finally, ask for a concrete plan for the first 30 days. If they cannot define their technical review workflow immediately, they will likely create technical debt and damage your brand.
While MQLs are useful as a diagnostic metric for top funnel reach, they are often misleading in the security space. Optimize your strategy based on SQL quality and attributed pipeline revenue. High MQL counts often include non buyers like researchers or students. True investor grade growth is measured by the velocity of opportunities created and the total revenue impact. See the section on RevOps and pipeline attribution above for the full breakdown.



